In this video, we learn how to use Visual Basic to convert temperature units. To start, make two command buttons. After you have created these, make sure you label them. The first command button should say "celsius to fahrenheit" and the second should say "fahrenheit to celcius". After this, make one text box and one label box. Now you will convert celsius to fahrenheit using the formula "F=(9/5*C) + 32". and you will be able to use this to convert temperature units. Save this and use it for ...
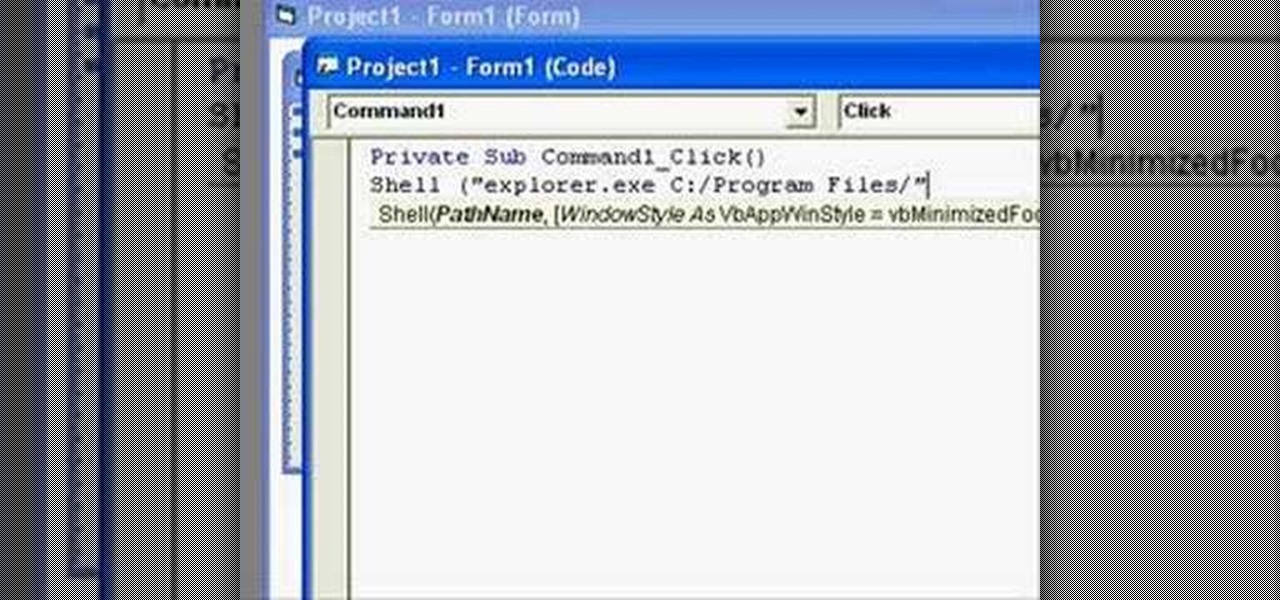
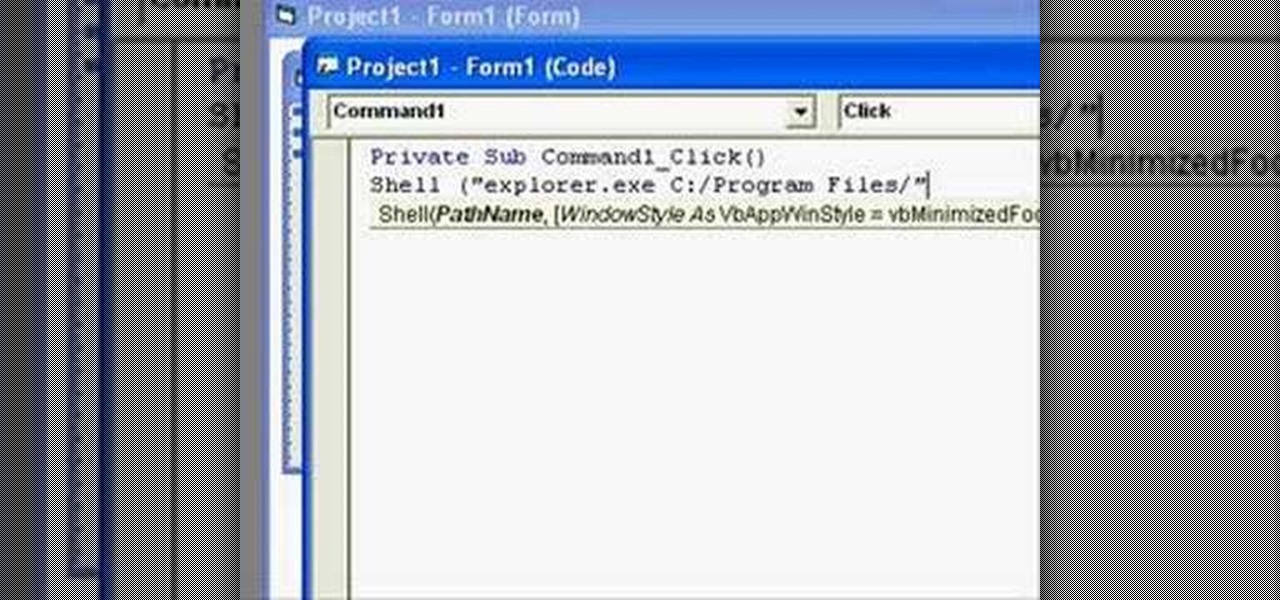
In this clip, you'll learn how to use the shell function to use the shell function to open folders. Whether you're new to Microsoft's popular event-driven program language & IDE or a seasoned developer merely looking to improve your chops, you're sure to find benefit in this free Visual Basic programming lesson. For more information, including a complete demonstration and detailed, step-by-step instructions, take a look.
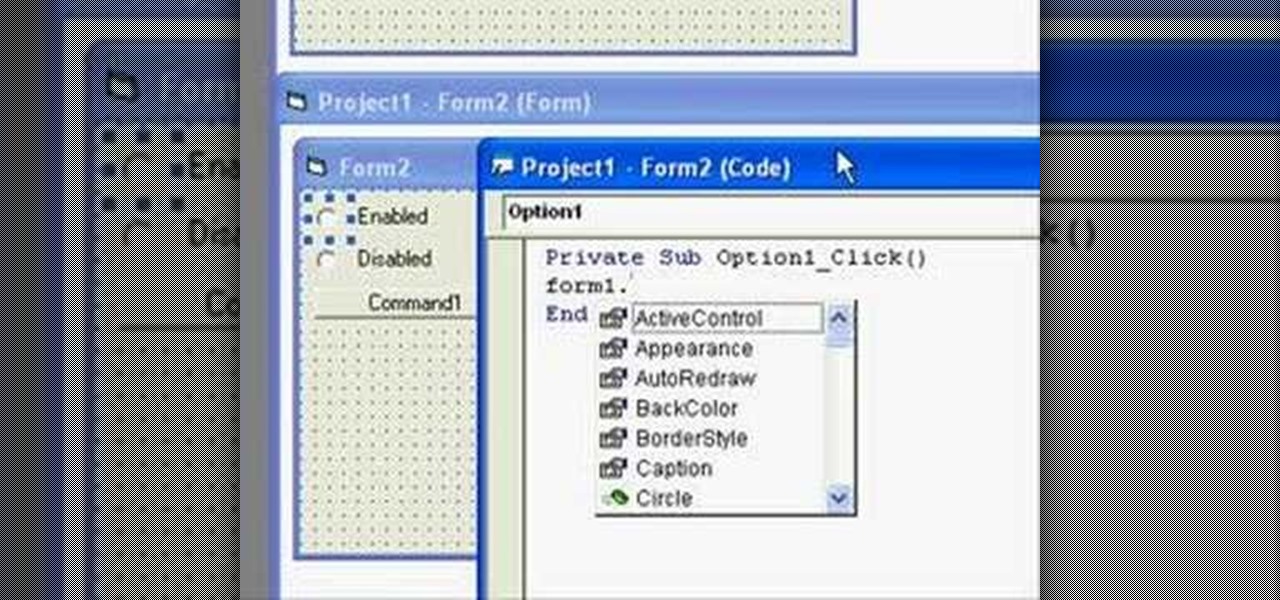
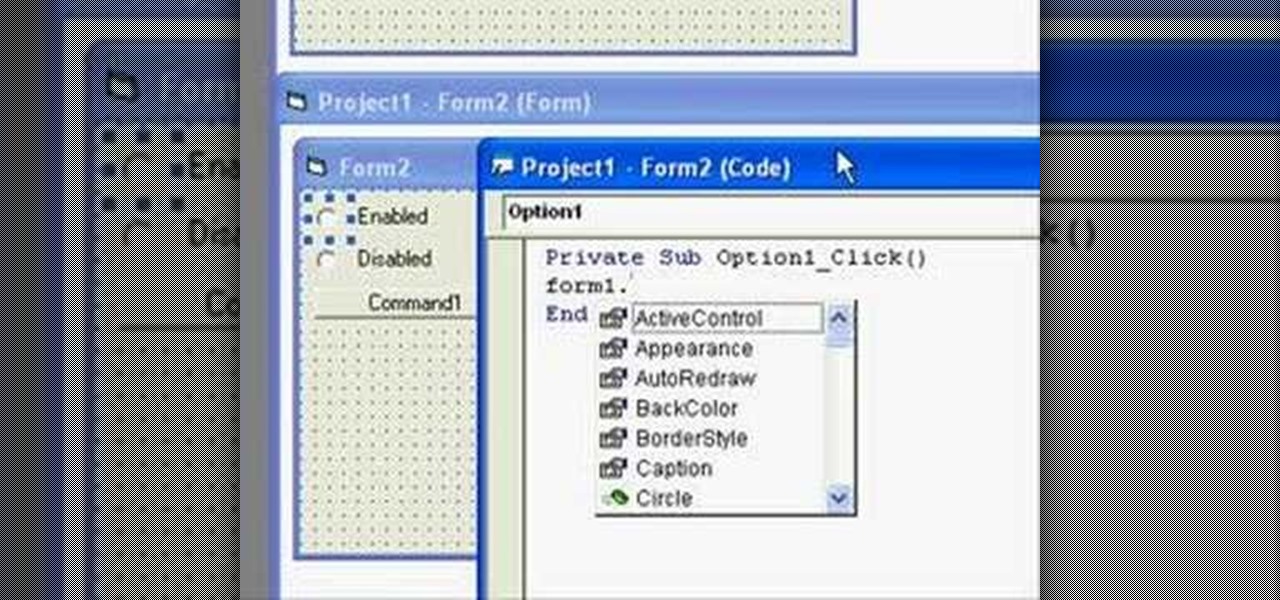
In this clip, you'll learn about basic form control within Visual Basic 6. Whether you're new to Microsoft's popular event-driven program language & IDE or a seasoned developer merely looking to improve your chops, you're sure to find benefit in this free Visual Basic programming lesson. For more information, including a complete demonstration and detailed, step-by-step instructions, take a look.
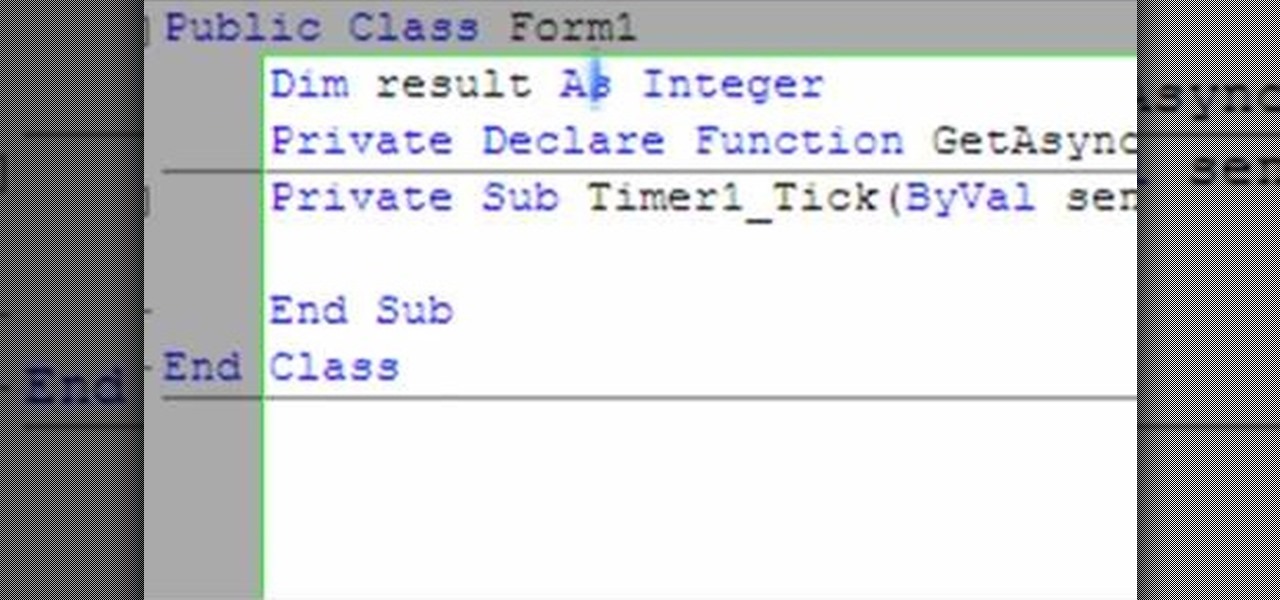
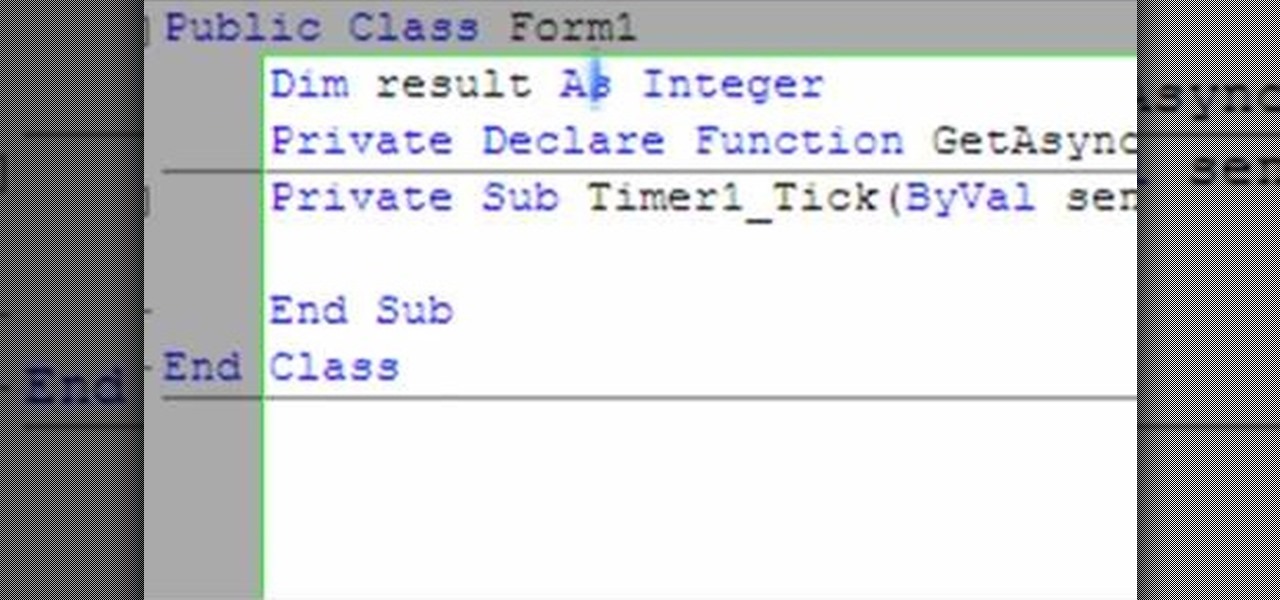
The following video shows how you can make a keylogger in Visual Basic 2008. Follow the steps below to create your own keylogger. First you will want to open a new application and name it according to your preferences. Then you want to click on the toolbar button and click textbox. In the textbox values, you will want to select the value of true for 'Multiline' option and the value of True for 'Read only'. On the toolbar, select the 'Behavior' tab and mark it as 'Window'. Go back on to the ma...

Oh, no! Visual Basic macros are no longer supported in Excel 2008 for Mac, which might make things a little difficult for you if you're used them a lot in the past, or if somebody else gives you spreadsheets using them. The Microsoft Office for Mac team shows you just how to deal with Visual Basic macros in this how-to video.

If you want to learn patterns drafting/making in different sizes (EXTRA SMALL, SMALL, MEDIUM, MEDIUM-LARGE, LARGE, EXTRA LARGE), now it becomes easy with these great videos that make patterns drafting easier and clearer.

As a side scrolling game, performing various jumps in Super Mario Run on your iPhone or Android is as vital as eggs in a breakfast buffet.

A step by step video tutorial that shows how to make a basic flat square knot hemp bracelet. Easy and fun!

Today we teach you how to apply basic eye shadow. Apply eye shadow is So Easy A Guy Can Do It!

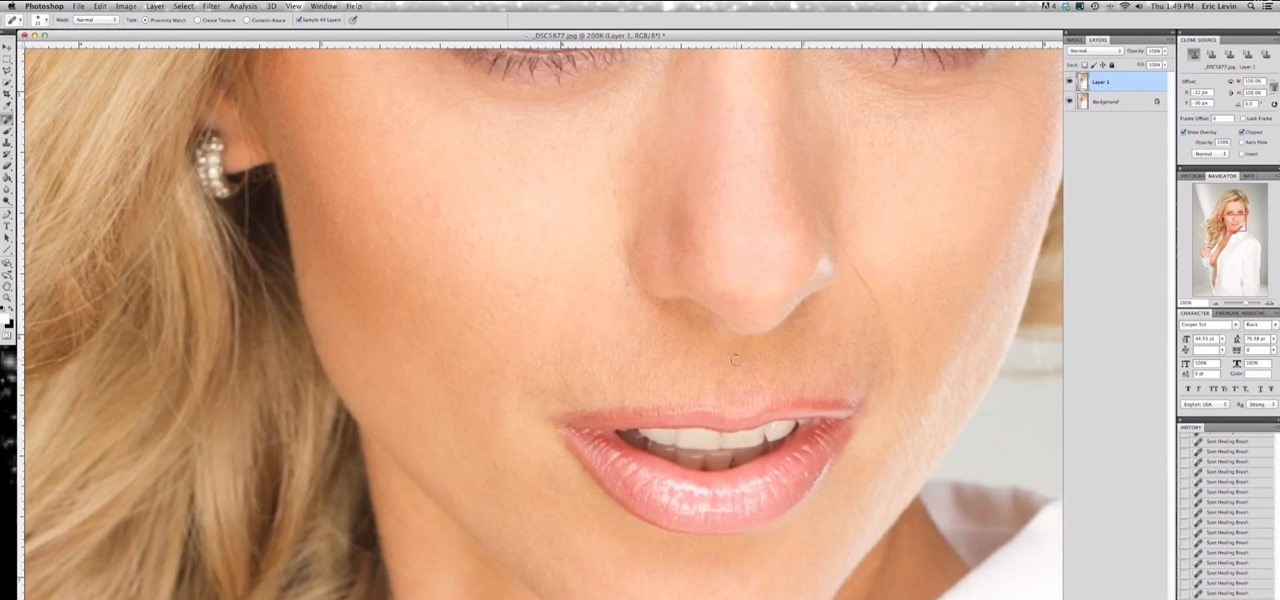
We had basic studio lighting, speed lights and photo shoots. This week The Elevin Show takes us on a Photoshop blitz to teach us a few skin retouching tips and tricks on Photoshop.

Welcome back everyone. This article isn't going to contain anything related to scripting, but rather some updates about the series. We'll be quickly discussing what we've covered so far and what is to come.

In python, or any scripting language for that matter, there are certain things that you will carry with you throughout your entire scripting career. Some of the most basic things that you will keep with you are output, variables, and their value types. We'll start by going over output, then cover variables and their types. So, let's get started!

Gardening school is in session and Shirley is teaching the absolute basics, such as: what to wear, what tools to use, what is the difference between an annual, perennial, and biennial? What is a garden zone, and which one is yours? Class is in session, so spit out your gum and listen up. Time to learn Gardening 101.

Welcome back, my tenderfoot hackers! As you should know from before, Snort is the most widely deployed intrusion detection system (IDS) in the world, and every hacker and IT security professional should be familiar with it. Hackers need to understand it for evasion, and IT security professionals to prevent intrusions. So a basic understanding of this ubiquitous IDS is crucial.

Welcome back, my greenhorn hackers! As expected with Null Byte's dramatic growth over the last year, we have added many new aspiring hackers who are still lacking in the basics of networking. In addition, with the new "White Hat" certifications coming out shortly, the exam will require some basic networking skills and knowledge to pass.
Hello, I'm a new guy around here and since I'm not seeing much tutorials in C i thought of contributing with something relatively simple. This will be a short series.

With any continuously active software, it can start to become fairly complex after a few years of updates. New features and revisions both get layered into a thick mesh of menu systems and controls that even pro users can get bewildered by. If you are new to a certain application after it has been around for many years, it can be downright intimidating to know where to begin.

Hair products can work wonders, but the good stuff is usually super expensive. Plus, most of the major brands use a ton of ingredients you can't even pronounce, so it's safe to say a lot of us have no idea what we're putting in our hair. The good side is that most products can be made at home using basic ingredients for a fraction of the cost of commercial brands. Hairspray is no exception, and actually one of the easier ones to make.

Welcome back! In the last training session we covered how to write and execute scripts. But today we'll be getting back to the code!

Managing hard drives in Linux is crucial to understanding your system and its operation as well as understanding the system you are exploiting or conducting a forensic analysis on. Linux has numerous commands that can provide us with information, control, and management of hard drives, and in this tutorial, we will examine a number of the most important ones.

Last time in how to train you python, we covered the basics of variables and output. While we were covering variables, we talked briefly about strings. "String" is just a fancier way of saying "Word". A string is simply a set of characters encased in quotations, this lets python know that it is a word. Sometimes when we do things with strings we'll need to change them in order to do something. Python is case sensitive, for example "Null-Byte" is not the same as "null-byte". This is where mani...

A simple video tutorial that teaches how to make these cute hemp earrings. Make a hemp bracelet and necklace to go with them for a matching set!

Hey guys, so today I am sharing a very special video in the memory of Talia Joy, as a mint mani for Talia as suggested by nail polish wars. Hundreds have already participated, and here is my version:

Video: . I have a new tutorial explaining the basic use of RayFire for 3dsmax.

Android 6.0 Marshmallow added a new permissions system that can make your digital life much more secure. Unlike previous versions, apps now have to ask for your consent before they can access certain data, which puts you firmly in the driver's seat.

I mentioned in 2015 I wanted to start a 'DoXing' series, and since I havent seen this on Null Byte, I am now going to introduce this to the community.

AppleScript is quite an easy scripting language to use. In this guide, I will be showing you several commands. Near the end, I will show how these can be used to create a fake virus that actually does no harm.

Greetings fellow students! I'm currently reading a book called "Violent Python: A Cookbook for Hackers, Forensic Analysts, Penetration Testers and Security Engineers"

Very often we have processes in Linux that we want to always run in the background at startup. These would be processes that we need to start at bootup and always be available to us.

If you're completely new to Android, you're in for a treat with all of the software tweaks and customization options that your smartphone or tablet offers out of the box. But if you really want to take things to the next level, the ability to mod your device expands exponentially when you're rooted.

In the last iteration of how to train your python, we covered basic string manipulation and how we can use it to better evaluate user input. So, today we'll be covering how to take user input. User input is very important to scripting. How can we do what the user says if we can't tell what the user wants? There are multiple ways to take input, we can give the user a prompt and take input from them directly, or we could use flags/switches, and take their input before the script is even execute...

Welcome back, my budding hackers! In previous tutorials, we've looked at some of the basic commands and concepts for using Linux. Along the way, I realized that I've failed to provide you with some basic background material on the stdin, stdout, and stderror.

Welcome back, my aspiring hackers! As mentioned several times in previous Linux tutorials, nearly everything in Linux is a file, and very often they are text files. For instance, all of the configuration files in Linux are text files. To reconfigure an application in Linux, we simply need to open the configuration file, change the text file, re-save, and then restart the application and our reconfiguration is applied.

Welcome back, my hacker trainees! A number of you have written me regarding which operating system is best for hacking. I'll start by saying that nearly every professional and expert hacker uses Linux or Unix. Although some hacks can be done with Windows and Mac OS, nearly all of the hacking tools are developed specifically for Linux. There are some exceptions, though, including software like Cain and Abel, Havij, Zenmap, and Metasploit that are developed or ported for Windows.

Whether you're white hat, black hat, or some shade in-between, navigating through a network is a core part of hacking. To do that, we need to be able to explore a network to discover the addresses of gateways, interfaces, and other attached devices. When ifconfig just isn't enough, you can steer your way around a network with a convenient tool called Ship, the script for everything IP.

This is a very simple and easy basic pearl nail design video that I wanted to share with you all! Hope you like it!

We all know that DNA is pretty amazing, but it's not something that most of us get much hands-on experience with. Even though it's in every living thing around us, we never see it, so we rarely think about it either.