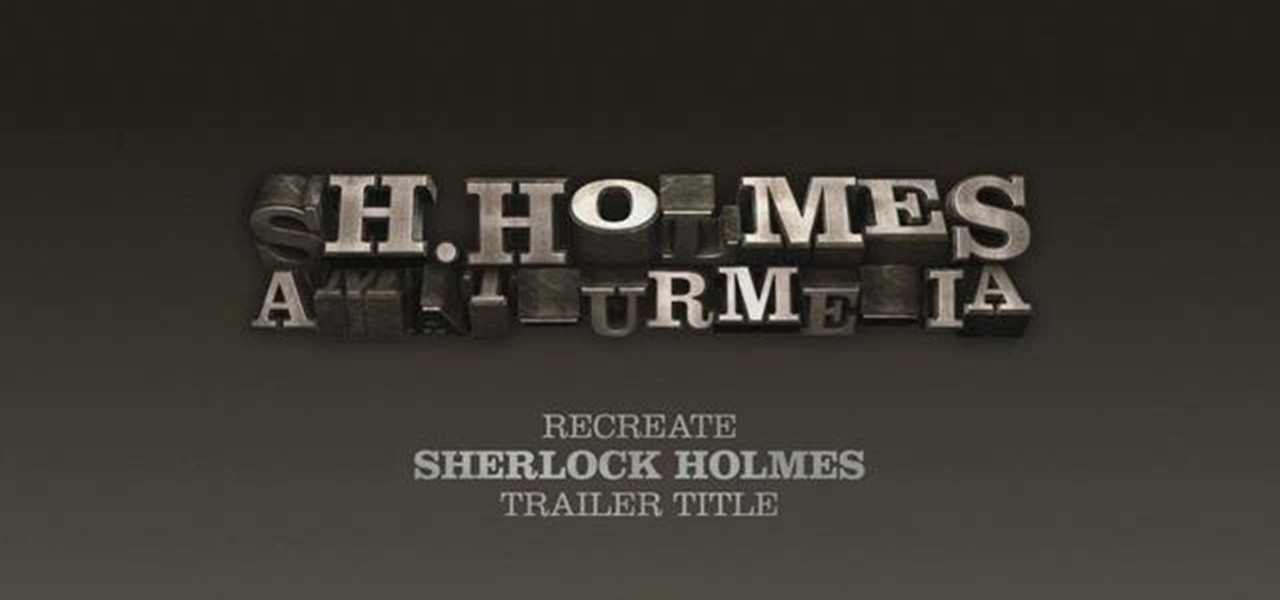
Want to recreate the look of the titles used in Guy Ritchie's 2009 adaptation of Sherlock Holmes? See how it's done with this Cinema 4D lesson. Whether you're new to MAXON's popular 3D modeling application or are just looking to get better acquainted with Cinema 4D and its various features and functions, you're sure to enjoy this free video software tutorial. For more information, including detailed, step-by-step instructions, watch this 3D modeler's guide.

Welcome to our Indiana Jones special. This week, we've been challenged by Eric Zala, the director of "Raiders of the Lost Ark: The Adaptation" to create an awesome face melt effect for cheap! This is probably Indy Mogul's grossest effect yet, so you better not get nauseous or anything, because you might just want to use this for your film!
3,2,1... blast off! Here's a fun little experiment you can do with a tea bag and some matches. You can try it at home and see how far up you can make your tea bag rocket go. The Tea Bag Rocket is really an adaptation of a classic science demonstration called the Ditto Paper Rocket. Each piece of Ditto paper had a sheet of tissue paper that separated the two-part form, and it was this discarded piece of paper that kids used to make the "rocket." Since Ditto paper is a thing of the past, scienc...

Learn how to play "Once Upon a Dream" from Walt Disney's Snow White wwith this free video piano lesson. This video guide presents a complete, step-by-step breakdown of the song and its chords. For more information, and to get started playing this popular Disney tune on your own piano (which is itself an adaptation of a famous Tchaikovsky number), watch this tutorial.

In order to grow Rhododendrens in a greenhouse, you will need the following: climate control, timers, misters, and thermostats.

Who better to serve as your Xbox LIVE avatar than the patron saint of all things frivolous—namely, the Joker from the Dark Knight adaptation of DC Comics' popular Batman series! This gamer's guide will show you everything you'll need to know to create and use a green-haired, Heath Ledger-style Joker Xbox LIVE character.

Quindim is a typical Brazilian Dessert made with eggs, coconut and lots of sugar. The dish was probably a Brazilian born adaptation of a Portuguese sweet, mixed with heavy African influences. In the African Banto language, Quindim means "Girlish Charms". This recipe is so easy I've asked my 7-year-old daughter to prepare it for you.

Welcome to the Everyday Dish vegan cooking show! This is a fabulous vegan adaptation of our favorite coffee cake. It never lasts long in our home as you can see!!!

Eyepatchentertainmen teaches you how to choose the best prime lens for Canon cameras, for video shooting. The faster the lens, the lower the light we need. The dark sequence was shot using a Nikon 15 mm 1.8 lens. Canon 50 mm 1.8 or the Nikon 50 mm 1.8 are good starting prime lenses. These run about 100 dollars. Sigma 30 mm 1.4 is a way up from that. After that there is the Canon L series primes, those are very good as well. Adaptation is also needed when you start using lenses. The most expen...

Sherlock Holmes is one of the most famous characters in modern history, and has appeared in film more often than any other character. No less than 78 different actors have taken their turn at portraying the enigmatic deduction machine in various mediums, and each has brought their own foibles to the role. Some of the names may even surprise you: Tom Baker, John Cleese, Peter Cushing, Charlton Heston, Christopher Lee, Roger Moore, and even Leonard Nimoy.

If you want to appreciate the value of microbes, look no further than a chunk of cheese. Because cheese roughly traces back to the Neolithic Era, we might say the earliest cheesemakers were the first humans to manipulate microbes—without even knowing it. Now, thanks to microbiologists and the long tradition of cheesemaking, we know a lot more about the microbes that make our favorite types of cheese possible.

Netflix is branching out into the comic book business, and it's summoning augmented reality via Facebook to make the first issue more magical.

Given Dwayne "The Rock" Johnson's blockbuster movie pedigree and the promotional power that usually accompanies his work, there's a certain predictable symmetry in the news that Rampage, a movie adaptation of the classic arcade game, has now become an augmented reality mobile app.

A modern iPhone is capable of running sophisticated, exquisitely-rendered games that rival titles on current-generation consoles. However, there is some value in classic video game titles, whether you grew up playing games on the Atari 2600, Nintendo Entertainment System, and Sega Genesis or not.

While the airline, casino, cruise, and hotel industries are asking for government bailouts during the COVID-19 pandemic, companies around the US are giving away its apps and services for a limited time. So while you're stuck at home, keep your mind off of coronavirus with free movies, TV, music apps, concerts, internet, fitness sessions, classes, and more.

As far as HBO is concerned, it's not augmented reality — it's Snapchat. The premium cable network is leaning hard on Snapchat's AR magic tricks to promote yet another series, this time for the adaptation of Philip Pullman's His Dark Materials series of novels.

After leveraging the well-known intellectual property of Rovio's Angry Birds for its first game for the Magic Leap One, Resolution Games is singing a new song with a familiar refrain for its next game for the augmented reality headset.

The first mobile augmented reality app out of the gate with support for Magic Leap One Creator Edition is Thyng, who is planning to release the headset version of the app later this year.

One of the most popular mobile games out there for kids has added an augmented reality mode that brings the titular character into the real world.

If you've ever wanted to hang out with a flying unicorn that sounds like actor/comedian Patton Oswalt, get ready to get Happy!

Global design and technology services company Tata Elxsi says it has licensed its advanced autonomous vehicle middleware platform "AUTONOMAI" to a "leading automotive OEM."

TIFF 2012 Wrap-Up - Pounds Personally Gained: 4.5

While the automotive industry is moving towards adopting AR displays in future models, BMW is already shifting into the next gear with its vision of the technology.

The Unity 3D engine is not only responsible for facilitating the creation of 60% of AR and VR content but it also plays a significant role in producing the immersive stories that increasingly push the boundaries of cinema.

It's the holiday season, and the tech industry is giving consumers several AR products and apps as gift-giving options.

Although all signs points to Microsoft releasing a new HoloLens in the coming days, the company is nevertheless looking to distribute its augmented reality apps to other operating systems.

Less than three weeks after Rovio Entertainment announced the game, the augmented reality adaptation of Angry Birds is now available for the Magic Leap One.

Being Jewish is kind of tough this time of year. Folks are putting up their lights, stringing popcorn and cranberries, and decorating trees. Those of us who don't celebrate Christmas start to feel a wee bit left out in the cold. Yes, some families give out presents on each of the eight nights of Hanukkah, but the truth is that it's not a major holiday on the Jewish calendar.

Since its creation, Arduino has been growing exponentially more popular as DIY enthusiasts and Makers alike realize its potential. As new versions of the device are released, many easy-to-use peripherals are showing up on the market also.

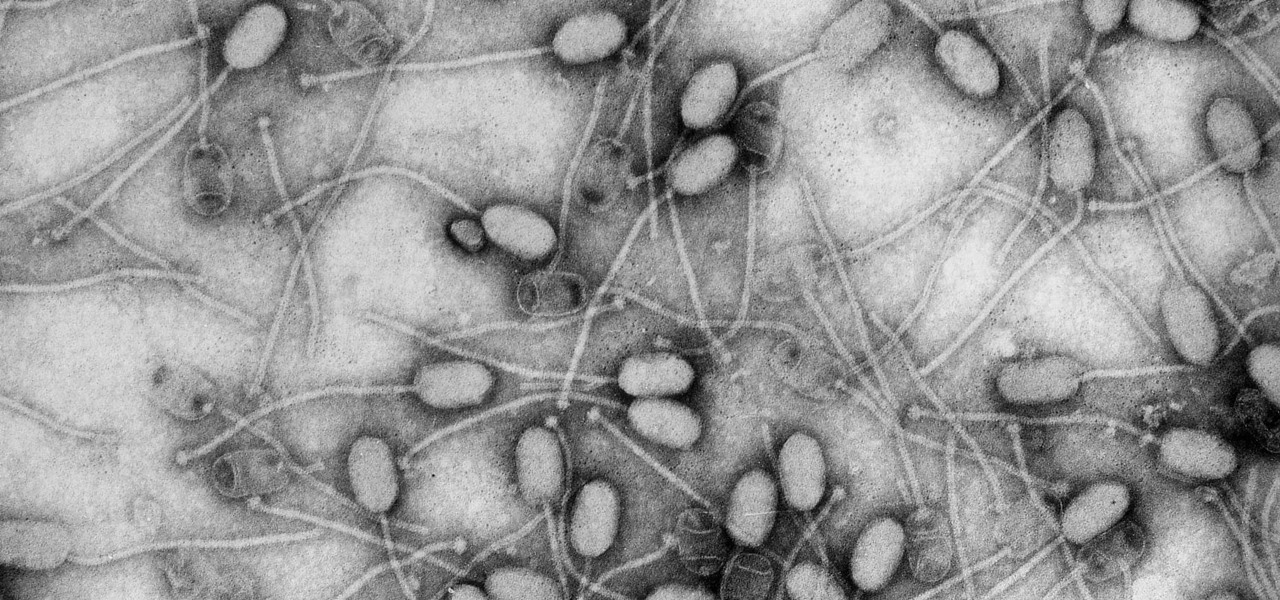
Fighting fire with fire, scientists are harnessing the adaptability of helpful microbes to challenge the adaptability of deadly microbes. What are we talking about? Hunting with phages — viruses that attack and kill bacteria.

The ability of one microbe to adapt is giving it a whole new career as a sexually transmitted disease. Usually content with the back of the throat and nose of those who carry it, the dangerous pathogen Neisseria meningitidis has adapted to cause an illness that looks a lot like gonorrhea.

The Great Barrier Reef in Australia is the largest living system on the planet. Yet more than 90% of the reef is bleaching because of the loss of a tiny algae that lives within the coral.

You might be familiar with the use of zucchini blossoms in cooking and maybe even know how to make herbal simple syrups. But if you really want to show off as someone who knows how to use flowering plants in food, try adding some flower water to your cooking/baking repertoire.

Staying inside during the coronavirus pandemic isn't easy for most of us. As important as it is to keep away from others, it can be challenging to keep to ourselves day after day. That's why mobile game developers are stepping in to help; many are making their games free for a limited time, to provide some much-needed fun during scary times.

Steampunk is a tremendously interesting phenomenon because of its reliance on science fiction, and fiction in general. Steampunk can arguably be broken down into two categories: the fiction, and the aesthetic. Sometimes these categories cross over, but they're often more distinct than most people suspect; that said, the aesthetic is firmly based in works of fiction.

With the tagline "More Than Meets the Eye," the Transformers franchise was pretty much preordained to have its own augmented reality game, and AR gaming pioneer Niantic has stepped up to fulfill that destiny.

Niantic first unveiled its AR cloud back in 2018, using it to enhance the immersive capabilities of its gaming portfolio.

Having found success in video games and a hugely popular Netflix series, The Witcher franchise is now on the hunt for the coin Pokémon GO has earned in location-based augented reality mobile games.

Tor is an excellent obfuscation network for web traffic, and while instant messaging over the network is very useful, it can be relatively difficult to configure. In this guide, we'll look at two synchronous communications platforms (instant messengers) which can be routed over the Tor network, Ricochet and XMPP.

Tossing an old Android smartphone with a decent battery into your hacking kit can let you quickly map hundreds of vulnerable networks in your area just by walking or driving by them. The practice of wardriving uses a Wi-Fi network card and GPS receiver to stealthily discover and record the location and settings of any nearby routers, and your phone allows you to easily discover those with security issues.