Microsoft Office files can be password-protected in order to prevent tampering and ensure data integrity. But password-protected documents from earlier versions of Office are susceptible to having their hashes extracted with a simple program called office2john. Those extracted hashes can then be cracked using John the Ripper and Hashcat.

Protecting the ball in water polo is key to playing a solid game. This water polo instructional includes many drills designed to improve 1-1 play. It includes tips for both the water polo defense and attacker on how to protect the ball in play. This also refers to TV clips of league and pro games to connect it to actual game play.
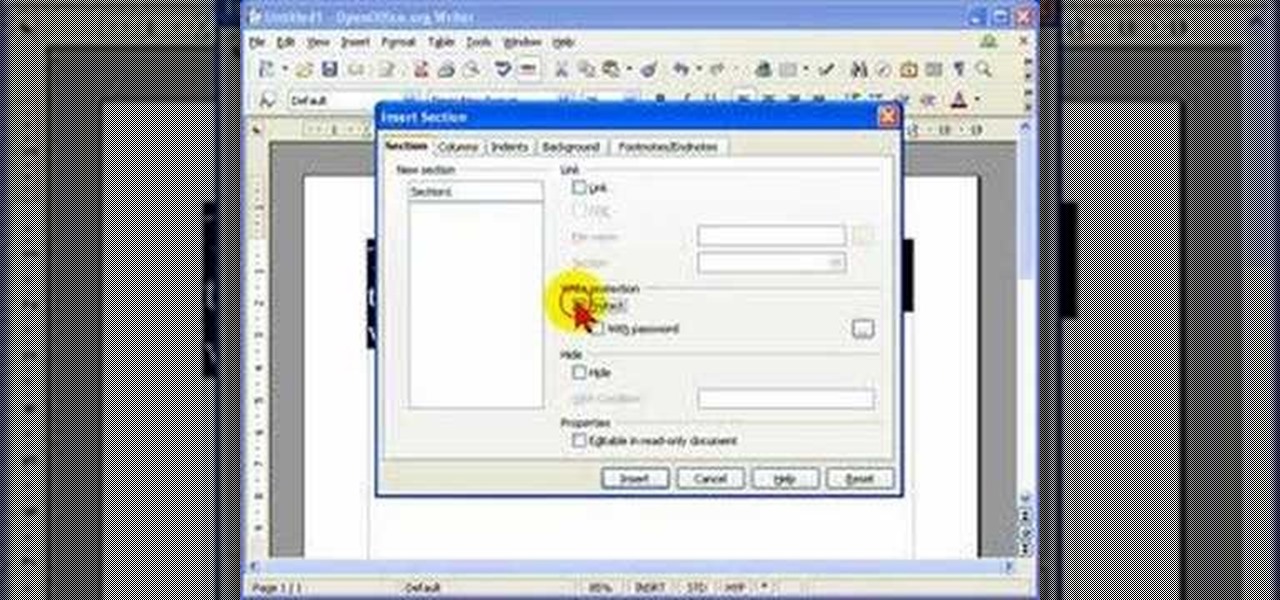
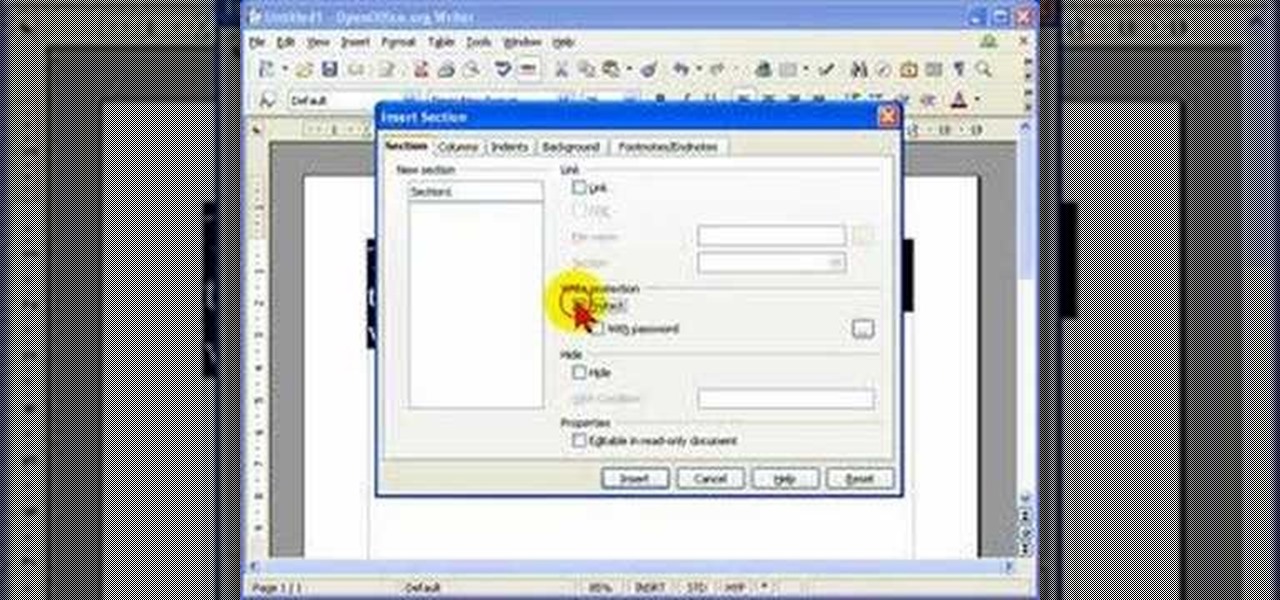
When you are editing your documents, it is sometimes a good idea to protect areas of text, so they cannot be edited, just in case you make a mistake and edit the wrong part.
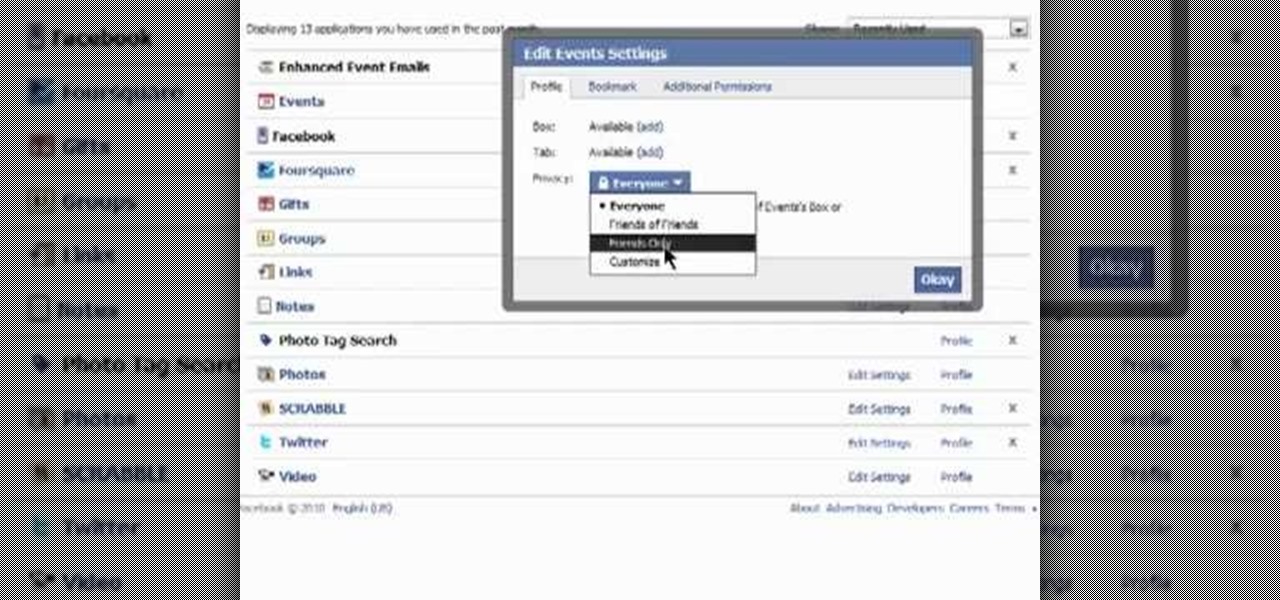
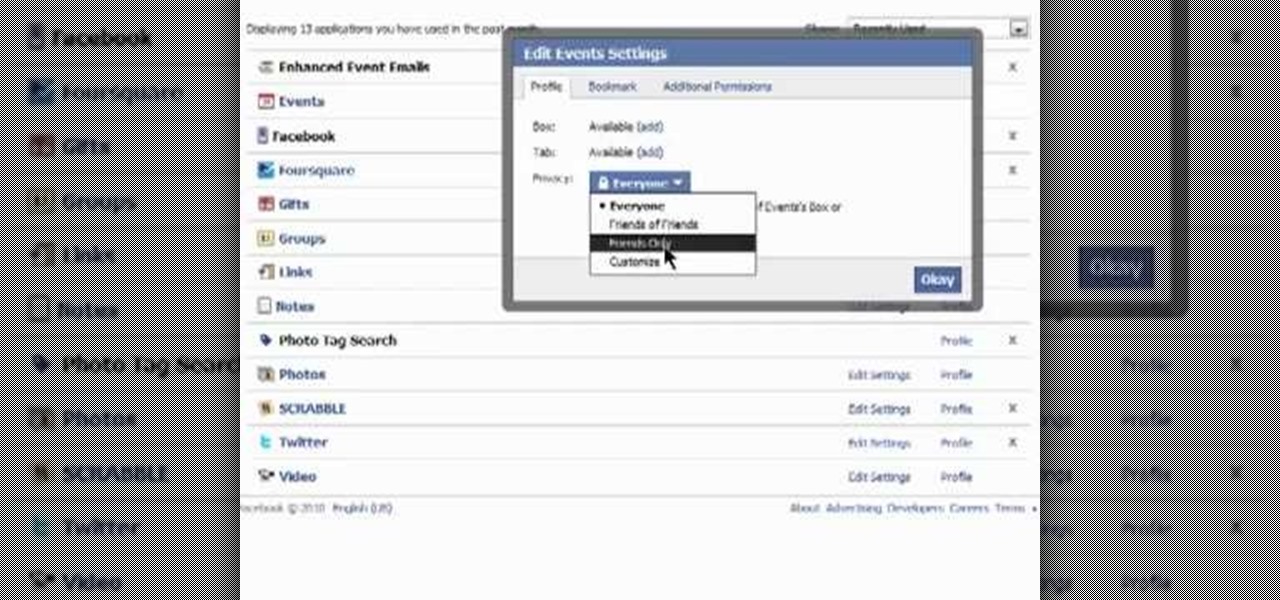
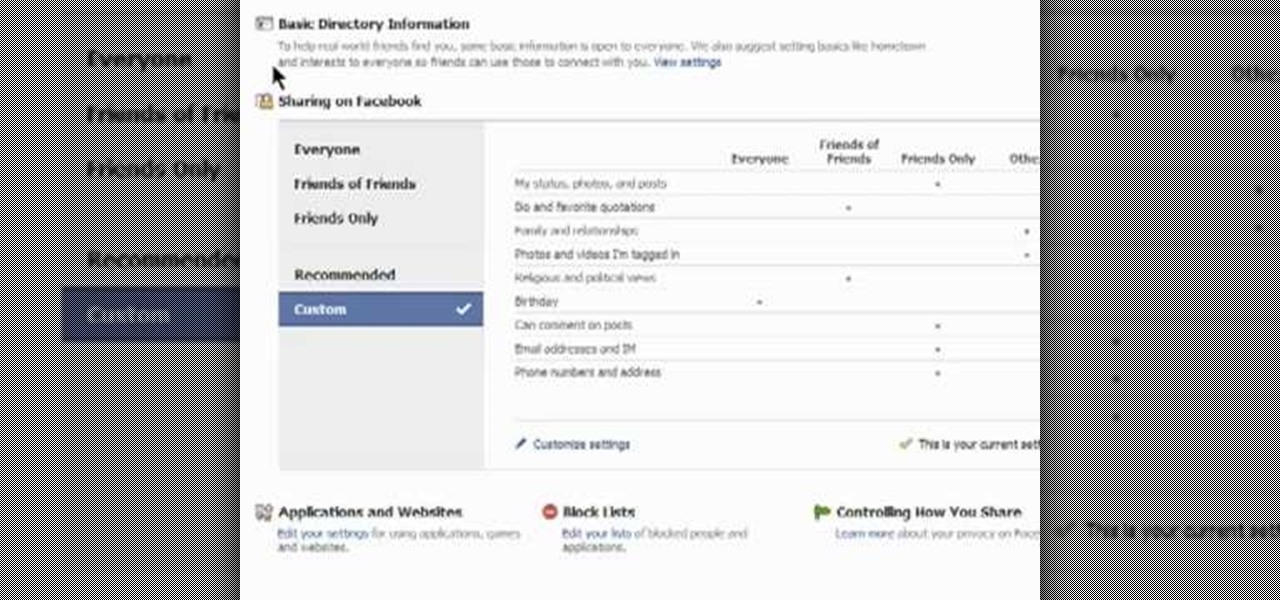
Need some help figuring out how to protect your privacy when using Facebook applications? It's easy! So easy, in fact, that this Facebook user's guide can present a complete overview of the process in about a minute's time. For more information, including detailed, step-by-step instructions, watch this guide.
In this clip, you'll learn how to secure a new Microsoft Windows desktop or laptop computer. For more information, including a complete demonstration, and detailed, step-by-step instructions, as well as to get started protecting your own new Microsoft Windows PC, take a look.
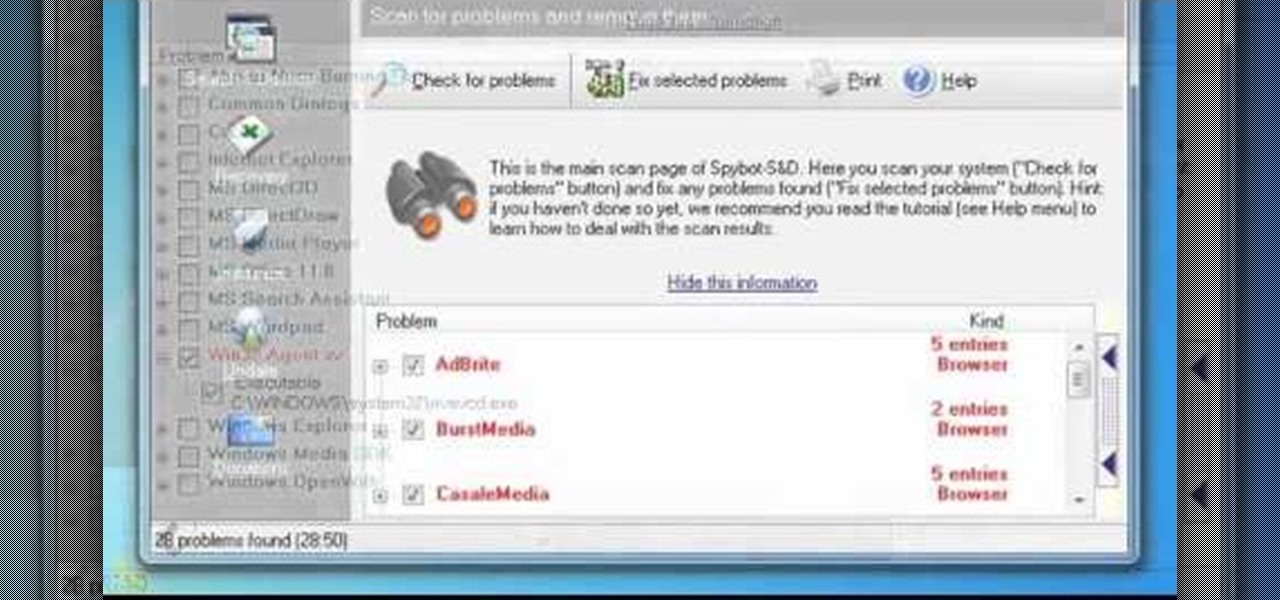
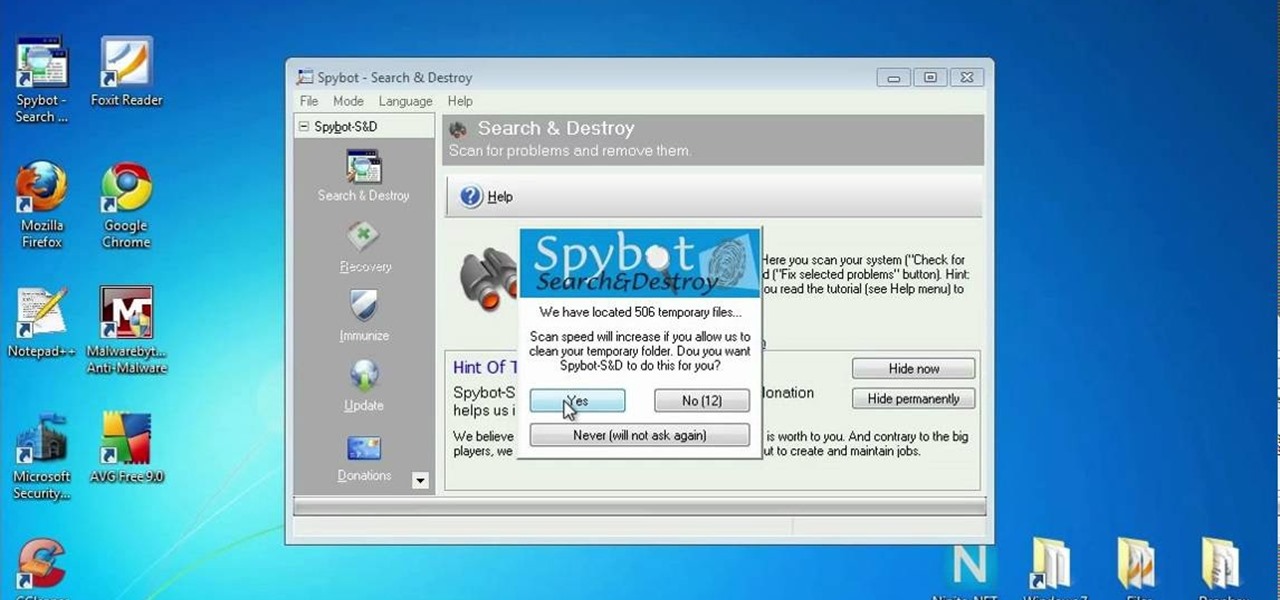
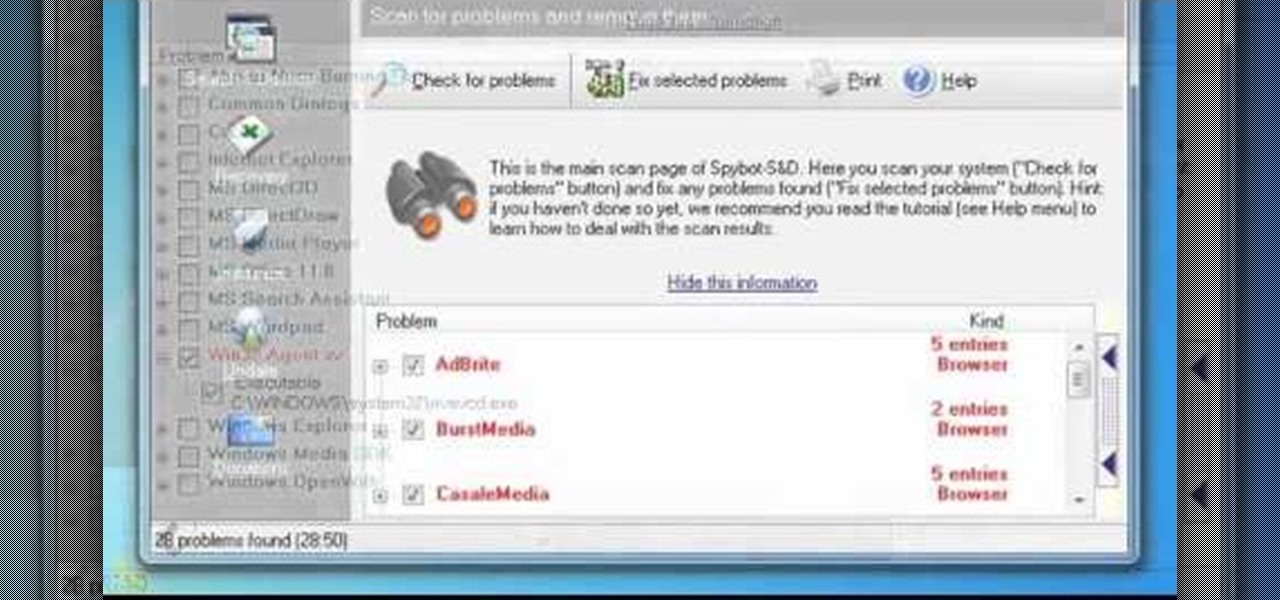
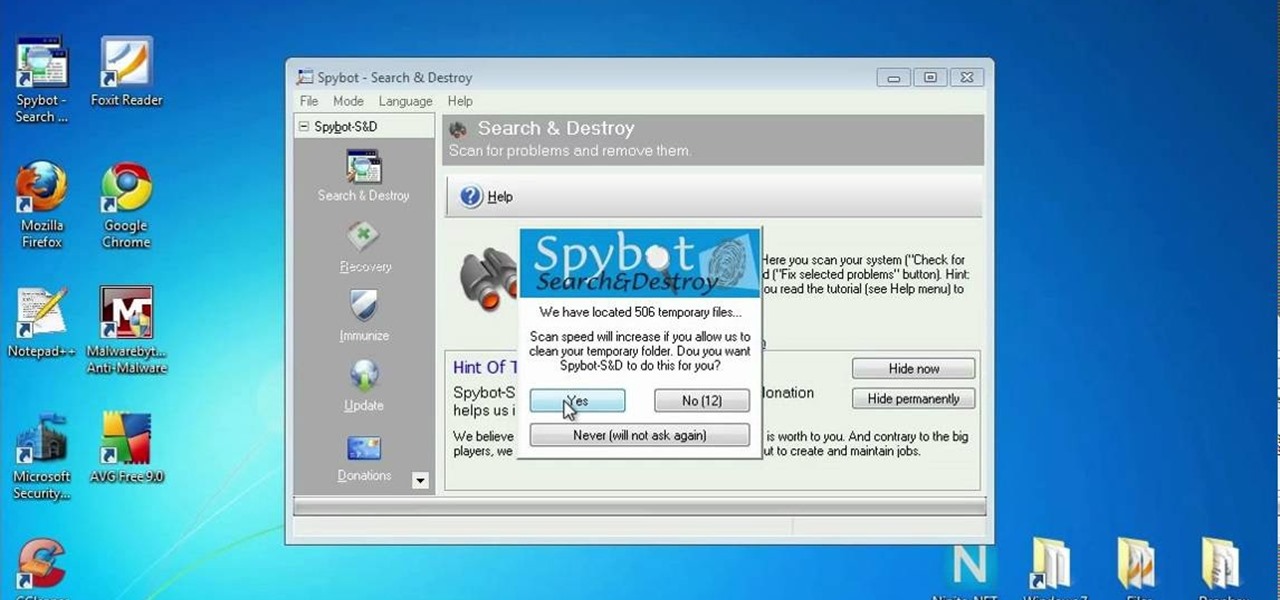
In this clip, you'll learn how to use the free Spybot Search & Destroy tool to protect against and remove malware on a Microsoft Windows PC. For more information, including detailed, step-by-step instructions, and to get started using Spybot on your own Win PC, take a look.

Looking for an easy way to protect your privacy when using Google Search? With the right habits, it's easy. So easy, in fact, that this home-computing how-to from the folks at CNET can present a complete overview of the process in just over a minute. For more information, including detailed, step-by-step instructions, take a look.

In this clip, you'll learn how to use the Backtrack 3 Linux distro and Aircrack-ng WiFi security app to crack the password to a WEP-protected wireless network. The process is simple. For more information, including step-by-step instructions, and to get started testing the security of your own WiFi networks, watch this hacker's how-to.

Interested in finding out just how secure your WEP-protected wireless network is? Let this video be your guide. It's a simple process and this home-networking how-to will teach you everything you'll need to know. For specifics, including detailed, step-by-step instructions, and to get started cracking WEP networks with BackTrack yourself, watch this helpful video guide.

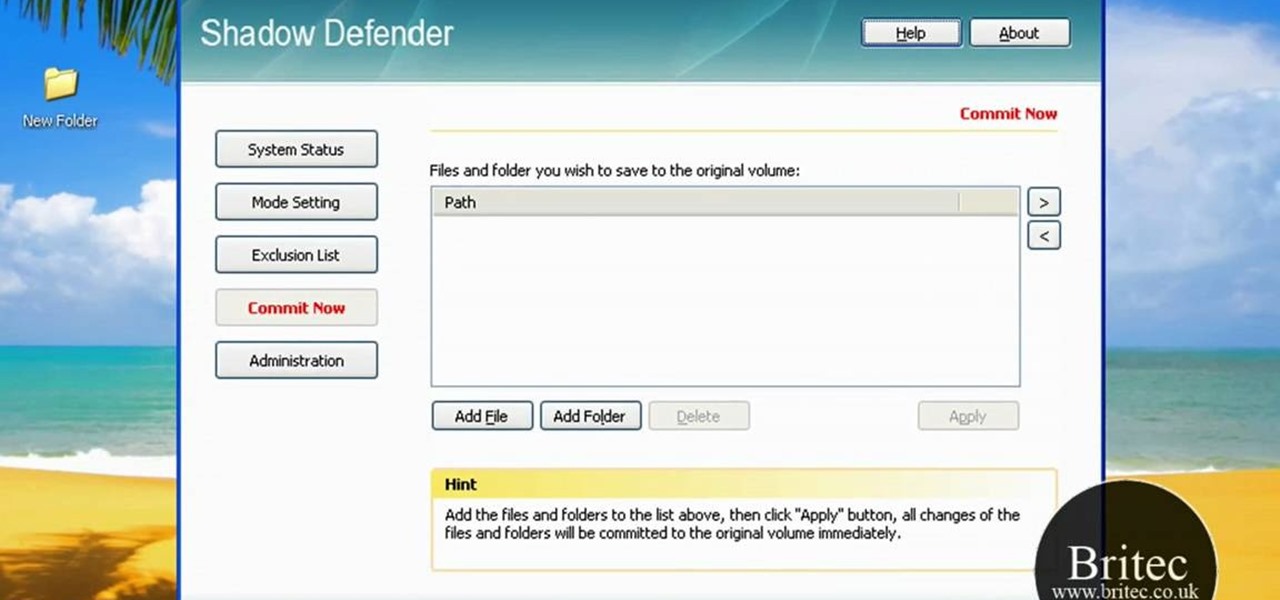
Looking for a security solution for your Microsoft Windows PC? With Shadow Defender, it's easy! So easy, in fact, that this home-computing how-to from the folks at Britec can present a complete overview of the process in just under ten minutes. For more information, including step-by-step instructions on how to get started using Shadow Defender to protect your own desktop computer or laptop, take a look.

Interested in making Firefox save your browser state more frequently to protect against crashes and outages? This clip will show you how it's done. It's easy! So easy, in fact, that this handy home-computing how-to from the folks at Tekzilla can present a complete overview of the process in about two minutes' time. For more information, including detailed, step-by-step instructions, take a look.

Learn how to use Smart Objects in Adobe Photoshop and how they protect your pixels when scaling images. Whether you're new to computer graphics, new to Adobe Photoshop CS4 or a seasoned design professional just looking to pick up a few new tips and tricks, you're certain to like this free video software tutorial. For more information, including detailed, step-by-step instructions, and to get started using Smart Objects in your own Photoshop projects, take a look!

In this clip, you'll learn how to get started using Symantec Backup Exec to protect SharePoint & Exchange servers. It's easy! So easy, in fact, that this helpful how-to can present a complete overview of the app in just under five minutes. For more information, including detailed, step-by-step instructions, take a look.

Protect your Windows desktop or laptop computer from malicious software with anti-virus applications. This handy how-to presents a complete overview of the process. It's easy! So easy, in fact, that this video guide can offer a complete overview of the entire process in just over four minutes. For more information, including step-by-step instructions, take a look.

Ever wanted to password protect a Firefox This clip will teach you everything you'll need to know. It's easy! So easy, in fact, that this home-computing how-to from the folks at Britec can present a complete overview of the process in just over two minutes. For more information, including detailed, step-by-step instructions, take a look.

Need to protect a section of your overall flash content (say movie or slideshow) from unauthorized access, learn how to do so in this video.

Looking for a primer on how to protect your Mac OS X desktop computer or laptop from malicious software? This clip for Apple amateurs will show you precisely what to do. You'll find it's easy. So easy, in fact, that this home-computing how-to can present a complete overview of the process in just over a minute and a half. For more information, including step-by-step instructions, take a look.

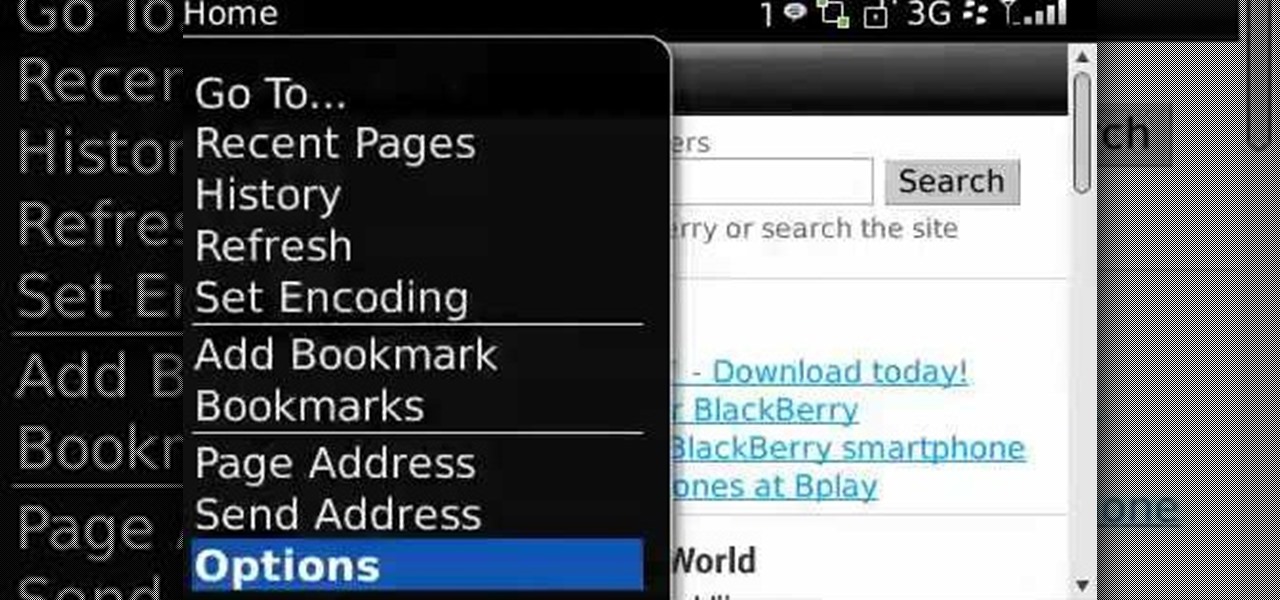
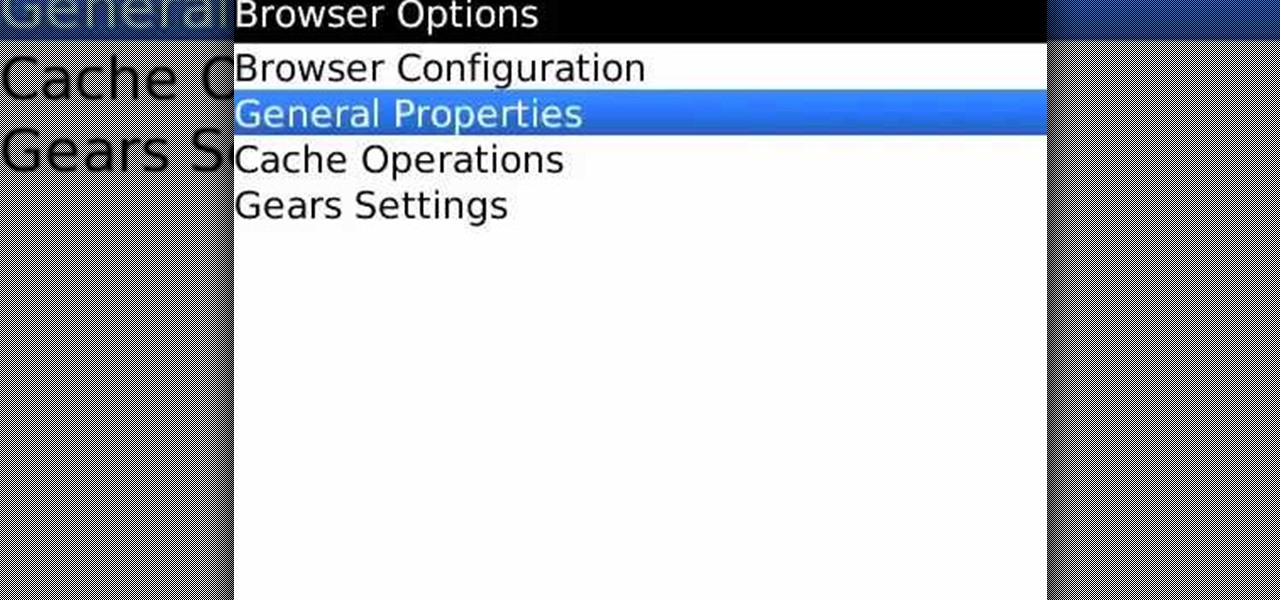
Protect yourself against would-be snoopers. Learn how to clear your temp Internet files on a BlackBerry phone. This clip will show you how it's done. Whether you're the proud owner of a BlackBerry smartphone or are merely considering picking one up, you're sure to be well served by this video guide. For detailed information, including step-by-step instructions, take a look.

Protect your privacy by deleting the temp Internet files on your BlackBerry phone. This clip will show you how it's done. Whether you're the proud owner of a BlackBerry smartphone or are merely considering picking one up, you're sure to be well served by this video guide. For detailed information, including step-by-step instructions, take a look.

This video talks about protected mode for internet explorer 7 and Windows Vista. The person tells you that protected mode helps protect your computer from types of spyware. It is not the best solution and they tell you one should not rely on this alone. By default protected mode is on. You want to make sure it hasn't accidentally been disabled. To check your settings, double click on the area on the bottom of the screen that says protected mode. The security tab will pop open. Look to see if ...

The Microsoft Office Access 2007 relational database manager enables information workers to quickly track and report information with ease thanks to its interactive design capabilities that do not require deep database knowledge. In this Microsoft Access video tutorial, you'll learn about creating a login form and password protecting your database.

Evergreen bows, like Hemlock, can be placed over tender plants to protect them against cold, winter winds. Gently place them over the plant creating a tepee or tent form. It will allow some air circulation underneath so the protected plant doesn't rot but the Evergreen bows protect it against the cold.

Protect your privacy by disabling Facebook Places once and for all. Whether you're completely new to the Facebook's popular social networking site or simply require a small amount of clarification on how to deal with the Places feature, you're sure to benefit from this helpful video guide. For more information, including detailed, step-by-step instructions, take a look.

Innoculate your Windows 7 PC against USB pen drive (Autorun.inf) viruses. This clip will show you how it's done. It's simple! So simple, in fact, that this home-computing how-to can present a complete, step-by-step overview of the process in just over three minutes. For more information, including complete, step-by-step instructions, take a look.

How to password protect a folder and make files invisible in Windows XP.

In the Colonist Mission of Safe Haven on Starcraft 2: Wings of Liberty, you'll have two choices, either to "Protect the Colony" or "Purify the Colony". This video will show you how to "Protect the Colony," because you want to make sure the Doc is pleased. Watch the full NextGenTactics campaign walkthrough to see all the action.

Smartphones are becoming pocket computers, jammed full of data essential to our personal and professional lives. With AT&T's 360 Backup app you can protect your important information with the push of a few buttons.

In this video tutorial, you'll learn about the risks associated with polysorbate 80, a common food additive. For all of the details, including a list of foods in which the additive is present, watch this video guide from Food Facts.

In this video tutorial, you'll learn about the risks associated with polysorbate 60, a common food additive. For all of the details, including a list of foods in which the additive is present, watch this video guide from Food Facts.

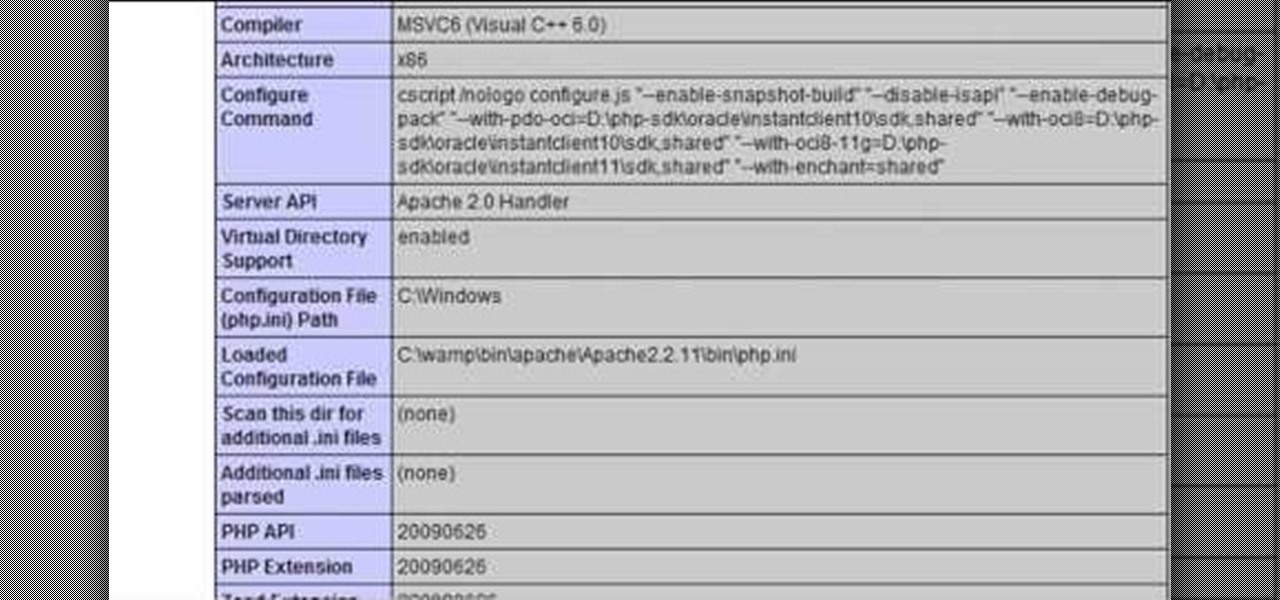
In this clip, you'll learn about how to prevent SQL injection when writing code in PHP. Whether you're new to the PHP: Hypertext Preprocessor scripting language or are a seasoned web developer merely looking to improve your chops, you're sure to find benefit in this free video programming lesson. For more information, including detailed, step-by-step instructions, take a look.

Protect your privacy by editing or completely erasing your Amazon search history. It's easy. And this brief video tutorial from the folks at Butterscotch will teach you everything you need to know. For more information, including detailed, step-by-step instructions, and to get started managing your own web pages with Google Sites, take a look.

Protect your privacy by using Google Search over SSL. With Firefox, it's easy! And this brief video tutorial from the folks at Butterscotch will teach you everything you need to know. For more information, including detailed, step-by-step instructions, and to get started using Google Search in SSL mode yourself, take a look.

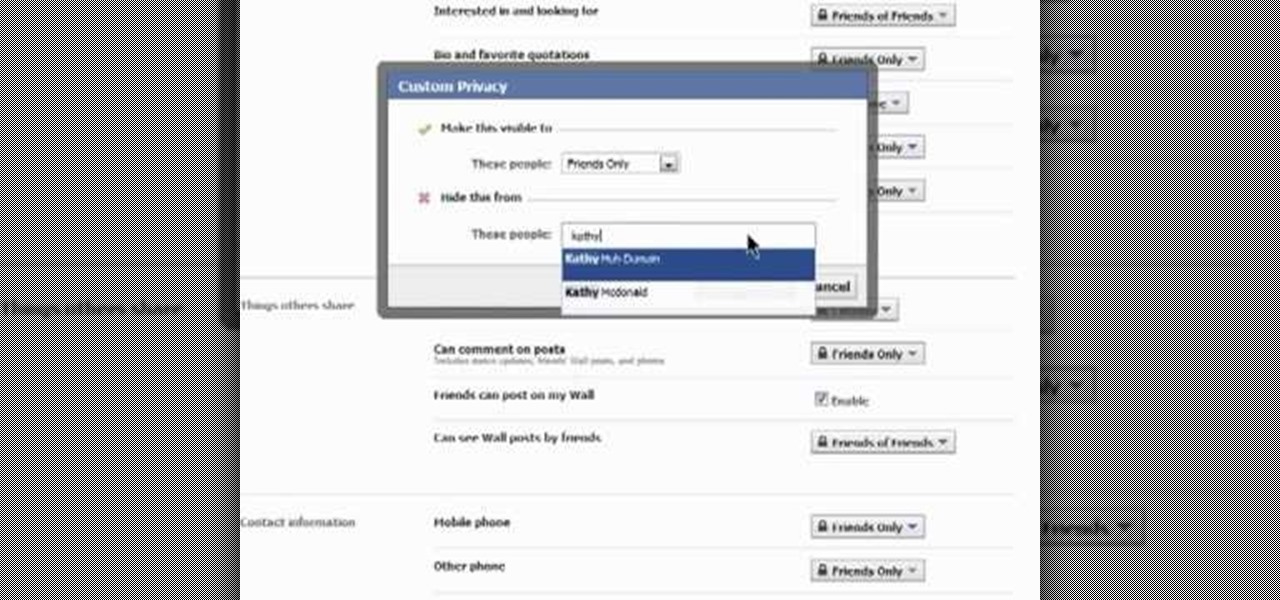
This clip presents an overview of the most important privacy settings on Facebook. Fortunately, with the right knowledge and the new Facebook Privacy Settings regime, protecting your data can be easy. So easy, in fact, that this video guide can present a complete overview of the process in about two minutes. For more information, including step-by-step instructions, take a look.

Protect your Facebook posts! This clip will show you how it's done. Whether you're completely new to the Facebook's popular social networking site or simply require a small amount of clarification on how to perform a particular task on Facebook, you're sure to benefit from this helpful video guide. For more information, including detailed, step-by-step instructions, take a look.

Want to change your Facebook privacy settings? This clip will show you how it's done. Whether you're completely new to the Facebook's popular social networking site or simply require a small amount of clarification on how to perform a particular task on Facebook, you're sure to benefit from this helpful video guide. For more information, including detailed, step-by-step instructions, take a look.

Learn how to construct a tin-foil tent to prevent your polymer-clay sculptures from burning as they bake. While this tutorial is best suited for those with some familiarity of polymer clay sculpture, novice sculpters should be able to follow along given a little effort. For specifics, including step-by-step instructions, and to get started protecting your own PC creations, watch this video guide.

Need to protect your school books? This free video guide has got you covered. With its help, you will learn how to make perfect custom book covers using a brown paper grocery bag. For more information, including step-by-step instructions on how to cut and fold your own custom protective book coverings, watch this handy how-to.

When you start a blog of your own you will want to make sure you protect yourself. Even before your blog takes off you will want to research trademark law when you attempt to register for a domain name.

Getting back to nature can be an incredibly rewarding experience – unless critters come along and ruin it! Here's how to keep your food from being plundered. To keep your food protected while camping out in the great outdoors, try bringing along a cooler, a cloth or nylon sack, a sock, some rope, and sealable, waterproof plastic bags. Keeping your provisions safe will decrease the risk of animal attack, and make your journey out into nature a fun experience.

In this two-part tutorial series from the Scrollsaw Workshop, Steve Good discusses how to finish scrollsaw projects–a process which, according to Steve, includes four steps: gluing, sanding, beautifying and protecting. Let Steve walk you through his finishing process with this tutorial.