This is a Cheat Engine guide on how to hack this flash game - B29 Assault. Kongregate Acheatment shows you how to hack B29 Assault with Cheat Engine (09/23/09). This B29 Assault cheat will give you infinite nukes and an invincible hack.

Snake cams have become the epitome of high-tech gadgets on television and in movies. In 24, Jack Bauer is always using a snake camera to check for terrorists on the other side of the door. The video game Splinter Cell has made the snake cam an integral part to Sam Fisher's arsenal. And almost every spy movie features its use at one point or another.

Most people can barely be bothered to carry their wallets all the time, let alone a survival kit. When they're all dead from a massive natural disaster or terrorist attack, you'll know you were right to watch this video and prepare an every day carry (EDC) kit that ensure you will have the tools you need to survive with you at all times.

» Homeland Security Report Lists ‘Liberty Lovers’ As Terrorists. A new study funded by the Department of Homeland Security characterizes Americans who are “suspicious of centralized federal authority,” and “reverent of individual liberty” as “extreme right-wing” terrorists. » British police get battlefield weapons.

They are after you from all over the globe. Looking for ways to exploit you. Ways to hurt you. Not political terrorists, but rather "info terrorists." Each month thousands of websites get hacked into and have hidden links inserted into the pages by people wanting their spam sites to rank highly in the search engines.

Take a trip into the past as Sam Fisher gets captured by terrorists in the Iraq War. Instead of playing as Sam, you'll be playing the part of Victor Coste — the only man Sam trusts. Find out how Coste saved Fisher's life in this walkthrough for the Diwaniya, Iraq (Mission 4). What happens that day in Diwaniyah? Find out.

Today's word is "thwart". This is a verb which means to prevent from accomplishing a purpose or a plan. For example, you can say "The police thwarted three terrorist attacks at LAX last month."

Find the biggest files on your computer ordered by size. Learn to order folder by filesize so you can find the ones harboring the most diskspace terrorists. Learn to clear up your private data automatically and wipe it clean from being undeleted.

Time compression done on the NYC apocalypse.

Here's the trailer for the "Skyjacking" Terrorist vs. Counterterrorist map that I built using redstone for bombs, timers and more features, along with the SDK Gun Mod. If you want to give the PvP map a try, you can download it here. The goal is to defuse 3 bombs within 10 minutes! The last bomb has 2 wires; cut one of them to win—they are randomly chosen by redstone...

A bug out bag, or BOB, is a prepared bag, usually a backpack, designed to sustain you for up to 72 hours while your escape wherever you are in case of a natural disaster, terrorist attack, or other catastrophe. This video will teach you everything you need to know to prepare an effective BOB that will help ensure your survival.

Poison Ivy is without a doubt one of the prettiest villains in "Batman" history, despite her whole kooky eco-terrorist thing and ensaring male victims (quite literally) in her vines. Yes, the lady has ripe green skin, but she's also got some sexy curves that make men's hearts go all aflutter.

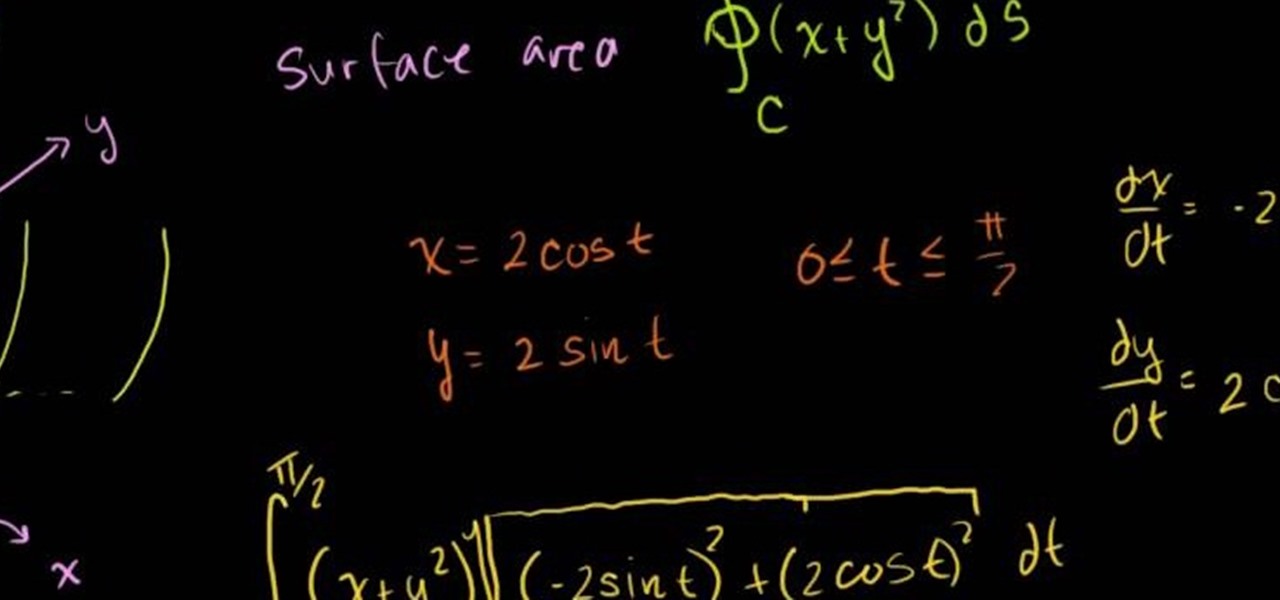
Line integrals will no longer be the feared terrorist of the math world thanks to this helpful guide from the Khan Academy. Marvel at the ease in which the integral is taken over a closed path and solved definitively. Then take out a sheet of paper and see if you can do the same.

Zip ties are stronger than they look, and escaping from them is tricky. In this tutorial from the folks at ITS Tactical, you'll learn how to quickly escape from zip ties. If you should ever find yourself kidnapped by terrorists, held for ransom or kept prisoner in a serial killer's basement, you'll be very glad you watched this video!

In a letter dated February 16th, Apple CEO Tim Cook responded to the FBI's demand that Apple create a "backdoor" to bypass the encryption on an iPhone used by one of the perpetrators of last year's terrorist attack in San Bernardino, CA. Cook began the letter by stating that Apple has "no sympathy for terrorists" and has cooperated in giving the FBI all of the information that it has available.

Watch this video tutorial to see how to make a ghillie suit, cheap and easy. But wait, what's a ghillie suit? A ghillie suit, or yowie suit, is a type of camouflage clothing designed to resemble heavy foliage. It's 3D camouflage, primarily used by military snipers and hunters, or to hide from terrorists. These camo ghillie suits include burlap and natural vegetation. Pull tall grass out, break down trees, hide yourself. Grab the burlap for less time consuming ghillie suit construction.
The Department of Homeland Security has been forced to release a list of keywords and phrases it uses to monitor social networking sites and online media for signs of terrorist or other threats against the U.S.

What if George Lucas had never created the Star Wars prequels, what if a secret terrorist organization had done it while they kept lucas locked away for 20 years in a prison cell.

The NYPD says it will launch an all-seeing "Domain Awareness System" that combines several streams of information to track both criminals and potential terrorists.
The Obama administration is moving to strengthen its ties with Persian Gulf nations whose geography and oil resources have already made them key players in U.S. defense and energy security.

The one man Sam Fisher trusts, Victor Coste, has some information for him. To find out the intelligence, Sam has agreed to meet in person. Find out what the important intel is in this walkthrough for the Washington Monument (Mission 5), and where that lead Sam next.

US can legally kill Americans in terror groups You read it right. The US can now target Americans who are supposedly part of terrorist groups. Here's my analysis of Attorney General Eric Holder points (keep in mind though, these are point's brought up by MSNBC, original article here):

WhatsApp sneakily made some security changes to iCloud backups without your knowledge, ladies and gents. Not that strengthening security is a bad thing, but still!

With the DOJ attempting to rip Apple a new one and an Apple attorney firing back, the President offered his opinion on the recent encryption debacle between the FBI and Apple at SXSW, amidst some talk about the direction of today's tech industry.

Welcome back, my novice hackers! Previously in my "Spy on Anyone" series, we used our hacking skills to turn a target's computer system into a bug to record conversations and found and downloaded confidential documents on someone's computer. In this tutorial, I will show you how to spy on somebody's Internet traffic.

People like Ralphige and The Jerky Boys have elevated prank phone calls to an art. Here’s how you can get in on the fun.

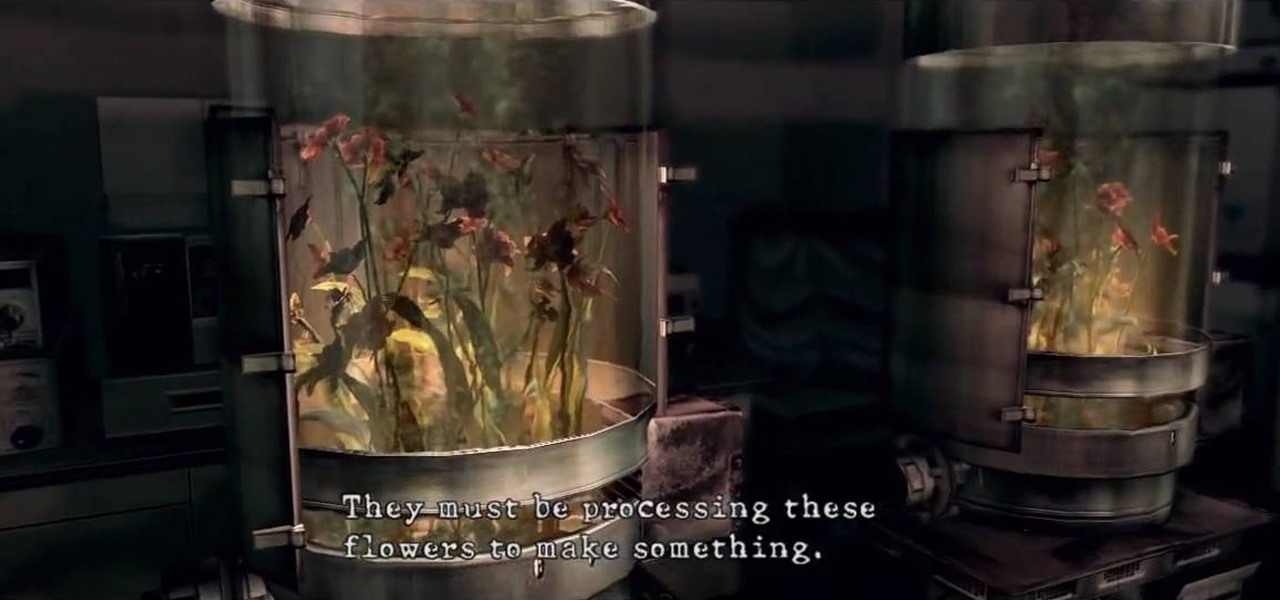
See Licker Beta and the U-8 Boss on this level of RE. See the playthrough for Resident Evil 5: Chapter 5-1, Underground Garden in this three-part video. The ruins appear to be adjacent to a large facility. Perhaps the answers Chris and Sheva seek can be found inside?

Racial Profiling at Boston Airport, Officials Say - NYTimes.com. Officers in an airport program intended to spot telltale mannerisms of potential terrorists say the operation has become a magnet for racial profiling. » The Next Election: High Stake Outcomes Based on Non-issues.

By now, nearly everyone with any type of media access is aware that Sony Pictures Entertainment was hacked on November 24th. Although there can be many interpretations and lessons drawn from this audacious act, there is one indisputable conclusion: it and its ripples across the globe underlines how important hacking has become in our all-digital 21st century. As I have emphasized so many times in this column, hacking is the discipline of the future. From cybercrime to cyber intelligence to cy...

The video is about tying a Zigzag braid knot design. At first, make the tag or rope into two by folding it. Take one end and make a small knot at the folded junction. Then take the second and pass it through the first made loop. Then take the other end and pass it through the loop made by second end. Continue the hitches to end the rope. Finish the knot by tightening the rope. Then rearrange the position of the hitches. This is done with care. The knot is made beautiful and prettier by making...

To make a Kinky Lover's knot, first hang or keep the tag on something. Then take the first end. Tie it by keeping a loop. Then take the second end and pass it through the loop by leaving a loop. Then take the second end, which was taken earlier , through the loop made by the first end. Then pass the second end through the loop, which was made by the second end. The knot is ready! All we have to do now is to tighten the knot by pulling the two ends. Make it beautiful by arranging the tag clearly.

This is a video demonstrating how to tie a perfection loop. This is a loop that is necessary for fishing. It can be using for sinkers and fly fishing. It is good for any purpose where a loop is needed. A loop is made first. The loop is held between the left thumb and index finger. The end of the line is taken and put over the loop. Then switch hands and take the end of the line below the main line, making two loops. Then the end of the line is placed between the two loops. Take the top loop n...

get a long piece of ribbon, put the ends together and make a crease at wear the ribbon folds, that'll be your center point. Now get one end of the ribbon, and without it flipping over, bring the end to the center of the ribbon and lay it perpendicular to the direction of the ribbon. Also bring the other end of the ribbon to the center of the ribbon but from the other direction. Hold the ribbon together using a gator clip. Obtain a piece of string or plastic strip, tie the folded ribbon tightl...

If you want to know how to tie a Double Windsor knot, this video is for you. To tie a Double Windsor knot: Lift up the collar of your shirt. Place the tie around the back of your neck so that the wide end hangs down on the side of your dominant hand, a little more than twice as low as the thin end. Cross the wide end once over the front of the thin end and then around the back of the thin end a few inches below your neck. Slip the wide end through the back of the V-shape made by the knot, pul...

Learn how to make an origami "orchid" by slightly altering an origami iris / lily flower. This origami video shows how to make what I call an orchid flower... really it's something I made by mistake when first learning to make an origami lily / iris. You'll need to start from the frog base.

Oh yeah, this is a big topic, at-least for me. All the frequent flyers will/should be interested in this topic. I'm sure all of you have heard at-least something about the TSA, and most of it should have been bad. Complaints, lawsuits and general disgust surround this organization. Is there a reason, or are the 'extremist liberals' at it again? Let's find out!

Will the predicted apocalyptic date—December 21st, 2012—really be the end of the world? In this ongoing five-part series, we examine what would happen if zombies, nuclear weapons, cyber wars, earthquakes, or aliens actually destroyed our planet—and how you might survive.

In this video, we learn how to use French wire when jewelry making. First, you want to take your wire and cut it to the length you need, using wire cutters. After this, you will place a stopper next to the pendant or bead that you are applying inside the necklace. Next, string on the clasp to the wire and then bend the end of the wire to the inside of the stopper, then cut the end of that with wire cutters. When finished, your clasp should be secure at the end of the wire and ready to hook on...

In this video, we learn how to tie a tie in ten easy steps. First, you will need to put the tie on and put the wide end in your right hand and the thin end in your left hand. After this, place the wide end over the top of the narrow, then put the wide end back over top the narrow end. Next, put the wide end through the loop made with the tie and your neck. After this, put the wide side through the front loop of the knot and pull the wide end down tightly. After this, hold the knot and pull th...

This video demonstrates how to tie a double Windsor knot, which is the neatest and most uniform looking tie knot. This knot can be tied in a few steps. First flip the shirt collar up and drape the tie around the neck as shown. Make sure to adjust the tie length so that the narrow end is just above the navel ring. Cross the wide end over the narrow end, pull the wide end back up the loop you just made, wrap the wide end behind the narrow end and back through the neck loop as shown. Pull both e...