
How To: Wind a bobbin
Your sewing machine needs bobbin thread to create overlock stitches, so keep your machine going by learning to fill your bobbin.


Your sewing machine needs bobbin thread to create overlock stitches, so keep your machine going by learning to fill your bobbin.
Create your own spinning picture frame with just a few dust-collecting items in your home! This video from Nextraker will show you how to build this interesting three-way picture frame, consisting of 6 open photo slots. You can simply put it on a hard surface, or you can make it spin 'round and 'round with a CD spindle.

In this video, Mark Sillay uses a unique grind on his spindle gouge and shows how he sharpens it. If you've never seen the Jool Tool sharpening system, you're going to be impressed.

What can you make from an empty CD holder? Check out this how-to video to make something amazing from those old plastic crappers... see how to recycle a plastic CD spindle into various uses. With this disc box, you can make a flashlight or torch, a food container, a string, yarn, or wire holder, and a tissue box.

This is a video tutorial in the Home & Garden category where you are going to learn how to fit door handles to a door properly. The first thing to do is to insert the spindle in the door and check if it is of correct length. Quite often it might be longer. So, cut it to the correct size with a hacksaw. Next fit the handle over the spindle and make sure it is straight. Take measurements to ensure this. Holding the handle in place with one hand, drill holes with an electric drill and insert the...

This video demonstrates how to build a fire with a bow drill. Your bow should be slightly curved. It should be the length of your arm. It can be fashioned from a tree limb and rawhide cord. You can use any number of types of cord. You will need a top rock. You will need a board. The board must be dry and dead. You will need a spindle. It should be the same type of wood as your board. You will also need a tinder bundle.

How to replace a tap washer. Dripping Tap. Dripping Faucet. Replacing a tap / facuet washer is quite an easy process as long as you follow the 6 steps in my video. Basically all you need to do is this:

This video demonstrates how to build a fire without using matches. For this, you will need the following: sticks, a leaf, and a tinder bundle.

This video will help you perform a rather elaborate piece of bicycle maintenance, overhauling and fixing a loose bearing in a Shimano Octolink pipe spindle bottom bracket. It is a long, complicated process that requires some specialized bike maintenance tools, but if you have these and are ready to increase the amount of maintenance that you are performing on your bike yourself, this video will walk you through the process in great detail and at a manageable pace.

Take a journey to the center of a vortex. A beautiful whirlpool is created by the magnetic coupler inside a tall CD cover, driven by the Tesla CD Turbine on faucet water pressure.

This how-to video shows how to build your own electric motorcycle; a nice way to change from gas to batteries to save the environment. There is lots of welding, but the key to welding is dropping the piece and checking if it stays together. Spindles and sprockets must align and then you are set. Check out this video customization tutorial and learn how to convert a motorcycle to electric power.

The FSA Mega Exo is a sophisticated integrated spindle external bearing crank. Like most elaborate bike products, it has several of its own quirks that make installing it different than installing any other similar product, like the Truvativ GXP. This video demonstrates the installation of the FSA Mega Exo system, listing all of the tools your will need and the step that you have to perform to integrate this high-performance part into your biking life.

The external bearing crank is just one of the complicated, necessary parts of a modern mountain bike. This video demonstrates the overhauling and installation of a Truvativ GXP integrated spindle external bearing crank. Without this video or a mountain of bicycle maintenance experience, this would probably be way beyond the skills of most bikers, but now you can install this exciting part on your bike yourself and reap the benefits.

The CD bubble trick. So simple, fun, and clever. Learn how to blow a bubble from a blank cd.

Make a fire with a bow and drill. Use fire birch for your spindle.

Recycle your plastic CD or DVD cases into a holder for parts. This tutorial shows you how to make your own container. Remove the spindle, then mount to a piece of wood. Once mounted, you can use this to hold and organize small parts.
Ruth demonstrates how to wind a bobbin successfully every time you attempt. Place the spool of thread on the machine and wind the thread between the two disks on the spindle (found in all machines). It is better to wind the thread twice to avoid the thread come off the spindle. This does not damage the machine in any way. Pull the thread towards the bobbin and pull it through the hole in thy bobbin inside-out. Place the threaded bobbin into the winder making sure the extra thread is on top an...

All you need to make this simple cable box is a plastic cd spindle and a pair of scissors. That's all. Then it's beautiful hidden cords all around.

Make a bow drill fire. Try resting it against your leg for stability.

A router table is a stationary woodworking machine in which a vertical spindle of a woodworking machine projects from the table, allowing you to cut wood at many different speeds. Different cutter heads or drill bits may be mounted on the router depending on the material you're working with.

Watch this video to learn how to spin to supplement your knitting projects. Use a ball bearing support spindle. It's very similar to spinning on a spinning wheel.

This video tutorial is in the Home & Garden category where you will learn how to install an interior door set on a pre-bored door. For this you will need a tube latch, straight plates, door plates, two knobs, two sets of ring guides and a spindle. You will also need a tape measure, ruler, screwdrivers, a drill and safety glasses. A pre-bored door has a face and an edge bore. First install the tube latch through the edge bore ensuring that the angle side of the tube face is towards the door ja...

The Tesla CD Turbine is a little homemade turbine made from CD's, CD spindle, supermagnets, and glue. It runs on faucet water pressure.
Freelance web developer and Internet marketer David Frosdick offers some tips and tricks in this video tutorial on how to secure your Gmail account.
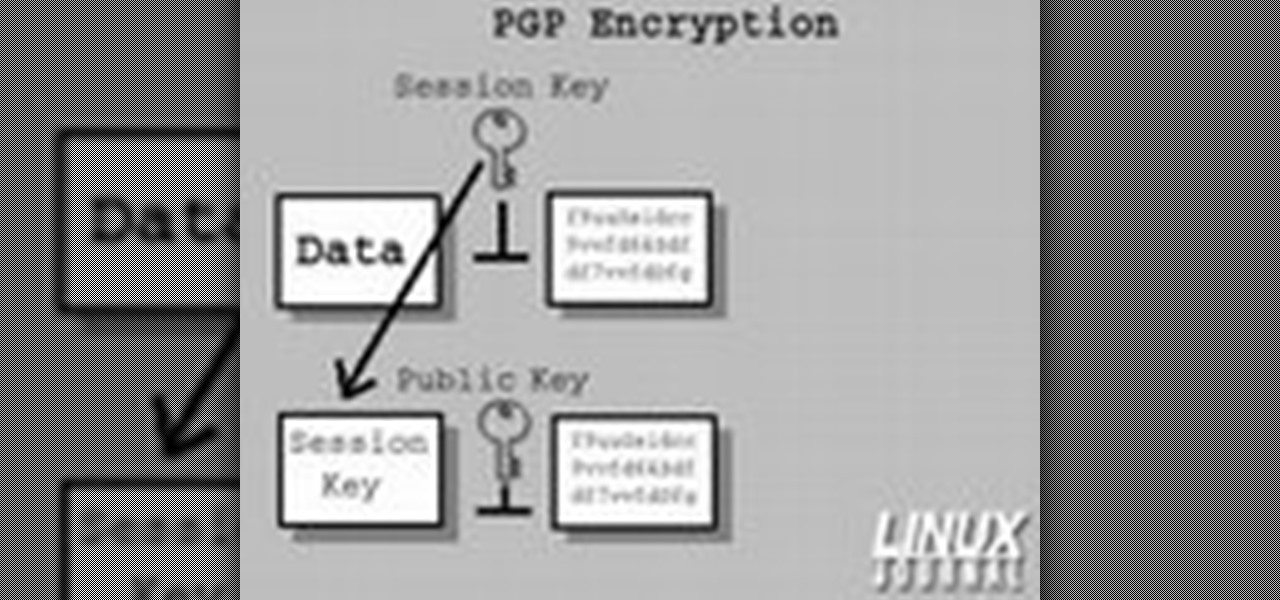
In today's time of rampant IT crimes, including identity theft, security is more important to the average computer user than ever. This tutorial, which was recorded and encoded for the Internet usingly only open source tools, demonstrates how you can use GnuPG to secure and verify data on your GNU/Linux box. Secure your Linux computer with this how-to.

Having a secure password is essential in today's interconnected world. Hackers are just around the corner, and if you have an easy to guess or hack password that you use for all of your accounts, someone can login to all of your websites very easily. Look at this guide on how to create a strong password by following the right password rules so that your accounts stay secure.

In this tutorial, we learn how to use salty hashes to keep passwords secure. A hash is stored in a database that is hashed with an algorithm, so not everyone can see exactly what your password is. When you type your password into a website, it doesn't actually register as words, it registers as a hash. This keeps your passwords secure so not everyone can see them. Salting is when you use random pits and attaching them to your regular hashes so not every password is the same. The salt is what ...

This new episode of Full Disclosure shows you how to use a SSH Tunnel to secure your data when you are on an untrusted LAN (ex. Coffee Shop, School's network, or Defcon). Furthermore, you can use the SSH Tunnel to bypass the LAN's internet filters. The SSH tunnel protocol works by encapsulates your data into an encrypted payload and transmitting it to the SSH Server which is setup on a trusted LAN.

In this clip, you'll learn how to get started using Secure Computing's Secure Web Protection proxy service. It's easy! So easy, in fact, that this helpful how-to can present a complete overview of the app in just over five minutes. For more information, including detailed, step-by-step instructions, take a look.

In this video tutorial, viewers learn how to secure a home wireless network. There are 3 types of security protocols for connecting devices. The 3 types of security protocols are: OPEN, WEP and WPA. Users should use passwords that are secure but no so obscure that they are unusable. The password should not be dictionary words. They should be mixed with casing and contain the user's phone number. Go to your router's website and log into the website. Find the setting for wireless security and e...

Have important files that you want to put on a USB drive but do not want anyone else to be able to access them? Put a password on it using USBSecure.net free resource.

Use three tools to create a simple ponytail. Use a hairbrush, a bobby pin, and a bungee band holder for this look. Using a bungee band instead of a standard ponytail holder eliminates some of the issues typically caused by pulling hair through ponytail holders. Start by using a bristled brush to brush the hair to one location on the head. Secure one hook of the bungee band in the ponytail and wrap the tail around the rest of the hair. Wrap it around again, and secure the other bungee band hoo...

Using ASP.NET Secure Services and Applications Services

Need to know how to tie a Bowline with a few ways of securing it? This way shows you how to secure it with a seizing so that it won't accidentally come undone. Included is a little variation of the bowline with a built-in seizing. If you don't have electrical tape to secure the bowline feed the bitter end back through the hole. It also makes it so you don't have a tail line dangling if you're towing something.
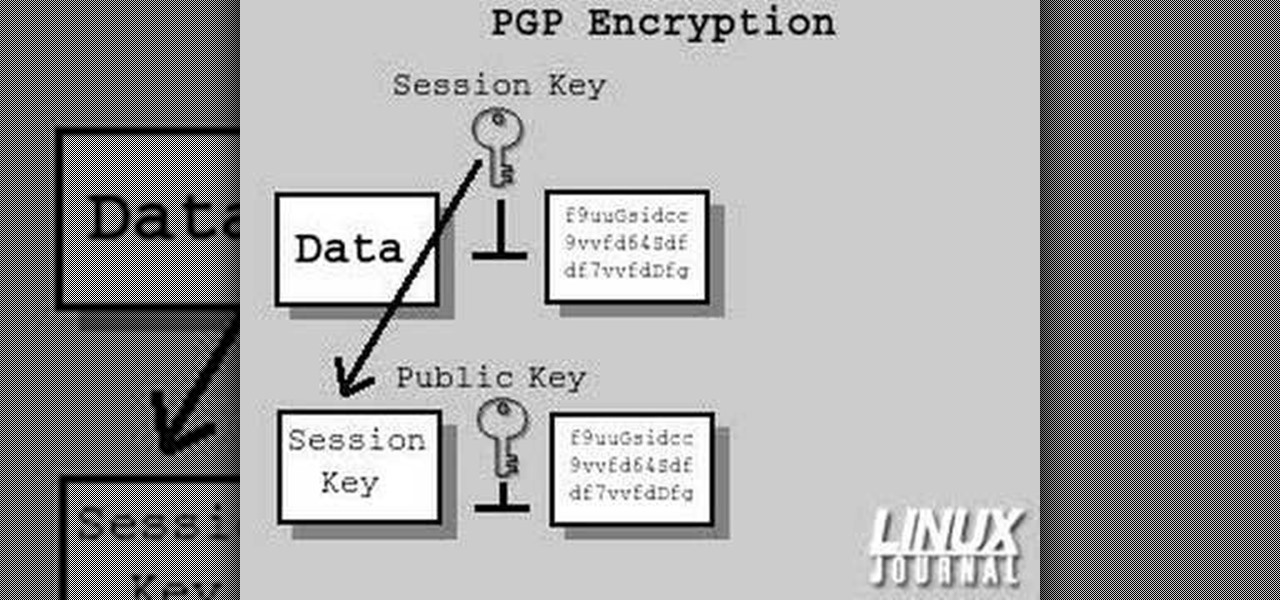
In today's time of rampant information crimes, including identity theft, security is more important to the average computer user than ever. This tutorial from Linux Journal Online shows how you can use GnuPG to secure and verify data on your Linux box. (This video was created using only free and open source software tools: TightVNC, pyvnc2swf, ardour2, audacity, jackd, LAME, kolourpaint, cinelerra-cv, mjpegtools, and ffmpeg.)

Buns and updos are gorgeous hairstyles, with one caveat: If they're not pinned perfectly and securely in place, all your hard work braiding and curling will go to waste as your hair slowly unravels.

Are you secure when downloading security software? Sounds like quite the conundrum, but CNET has answers. See if you're really secure when getting that software, and telling the difference between a rogue antivirus website versus a legit site. See how not to get scammed and destroyed!

Secure a square knot with tips from this video.

Don’t play Russian roulette when it comes to your wheels. Keep your bike secure with these precautions.

A formal occasion calls for a classic look. You Will Need