This square dance video teaches the following square dance calls on the mainstream list: Ocean Wave, Swing Thru, Run (Boys, Girls, Centers, Ends), Pass the Ocean, Trades (Boys, Girls, Ends, Centers), Dive Thru, Extend.

This square dance video teaches the following square dance calls on the mainstream list: Cross Run, Left Swing Thru, Single Hinge, Separate, Trade By, Wheel & Deal (Lines of 4).

In this video, the instructor shows how to schedule tasks in Microsoft Windows XP. Scheduled tasks are nothing but programs you want your computer to run at specific reoccurring intervals like daily, weekly, monthly, etc. This can be a very helpful feature if you want to update a particular software or run a system virus scan at regular intervals. To do this, click on the start button and go to run. In the Run command prompt, type in 'tasks' and hit enter. Now this opens up the schedule tasks...

Here's a quick tip for Android phone users! You can use the App Launcher (the icon is at the bottom of your phone, near the center) to open up your app screen, listing all your apps. From there, run all your favorite Android apps!
You don't have to have a smartphone to use Google Voice, but there are certain advantages if you do, including having your Google contact list at your fingertips. In this clip, you'll learn how to install and run Google Voice on most any smartphone.

Bring your favorite software, files, and settings with you on a USB drive

Brute-forcing is an easy way of discovering weak login credentials and is often one of the first steps when a hacker finds network services running on a network they gain access to. For beginners and experienced hackers alike, it's useful to have access to the right tools to discover, classify, and then launch customized brute-force attacks against a target. BruteDum does it all from a single framework.

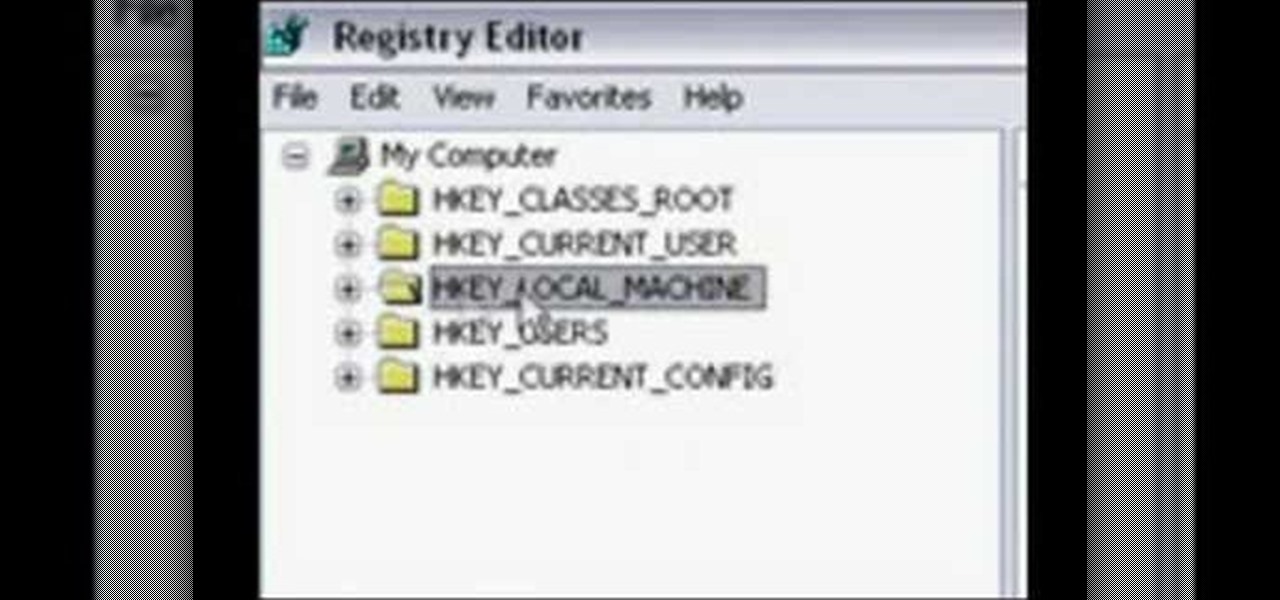
Steps adopted to bypass Windows Genuine Advantage Notification in Windows NT are:1. Open my computer2. Open the Local Disk (Where the Operating system is currently installed).3. Open windows folder and enter into the folder, system 32.(Shortcut: My Computer>Local Disk C>System 32)4. After entering system 32 (Folder), find and delete the file-wgatray.exe5. After deleting wgatray.exe file, go to the start menu and launch the run application6. In run, type in regedit and click OK,7. In regedit, ...

Accessing and getting in touch with your favorite contacts has never been easier thanks to the "Friends" feature on the Apple Watch. However, this only applies to users who are running watchOS 2.2.2 and lower. When Apple issued watchOS 3, the "Friends" option was completely removed. So if you're running watchOS 3 or higher, you won't be able to follow these instructions.

In this how to video, you will learn how to install fonts on to a computer running Windows. First, go to the start menu and go to control panel. From here, double click on fonts. Next, select install new font. From here, browse your folders to the folder you have saved your downloaded fonts. Once it is selected, press okay to add the font to your current list of fonts. You can check if the font can be used by opening up Photoshop. Create a new file and then press the text icon. From here, you...

Ready to make a statement in your town and get involved? Check out this tutorial and learn how to run for mayor. If you can't beat city hall, why not join it?

Bucky from The New Boston serves up this Python video tutorial on how to program lists functions in Python. This is the program you use to write all of your Python code down. Fun with list functions!

Sometimes you need a password to gain access to an older running Windows system. Maybe it's a machine in your basement you forgot about or a locked machine that belonged to a disgruntled employee. Maybe you just want to try out your pentesting skills.

When opening a link or sharing a photo, your Android device will bring up a list of possible applications that you can complete the action with. However, some of the apps included you never use or didn't even know existed, and this leads to unnecessary clutter. Fortunately, if you're rooted, there's an easy way to remove apps from the "Open with" and "Share via" lists.

PowerPoint 2008 for Mac can help you turn boring old bulleted lists into something nobody would forget. With SmartArt graphics in PowerPoint you can now make your bullet lists pop using pre-formatted charts, graphs, and more. The Microsoft Office for Mac team shows you just how to make a bulleted list more visual in this how-to video.

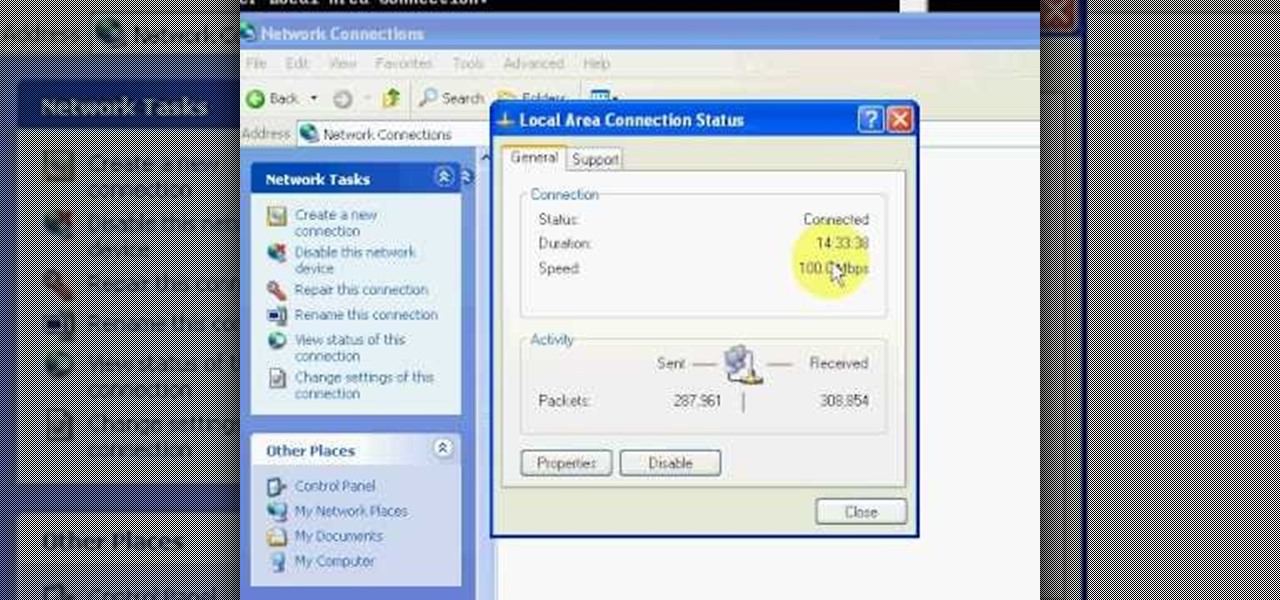
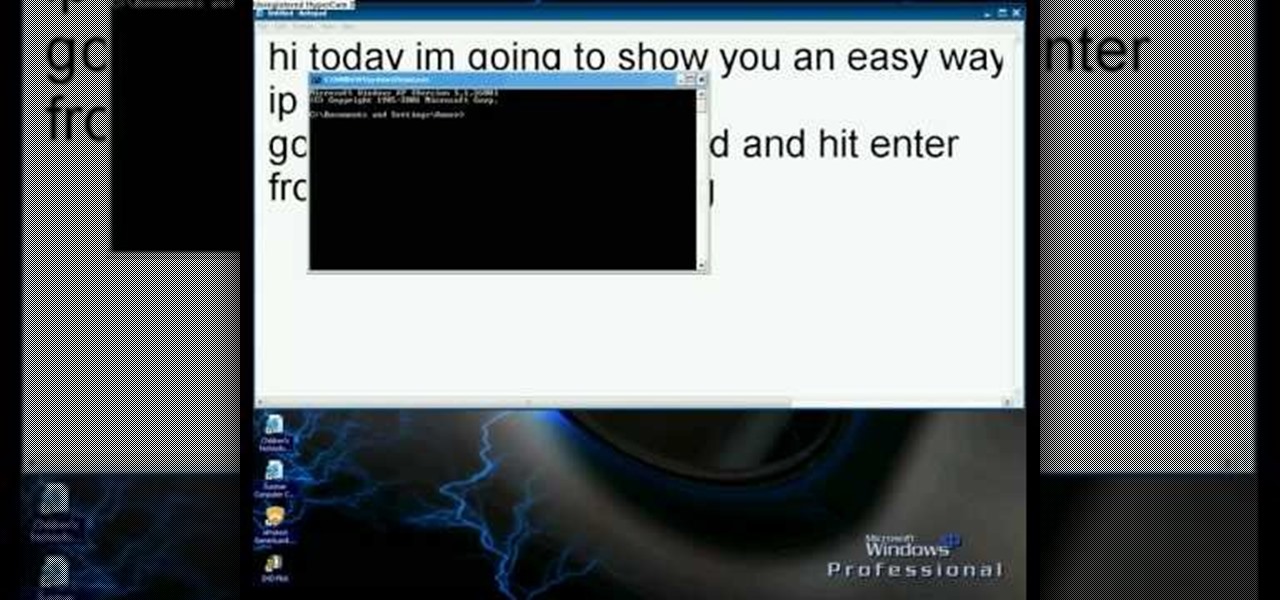
This video will show you how you can easily find out what your IP address is for a computer which is running the Windows XP operating system. You will first need to go to the start bar and click on the button which says "Run". Choose to run a program called "cmd" by typing this into the bar that appears. This will then open up a black box, where you should type in "ipconfig/all". Typing this in will offer you a list of information about the internet service you are currently using and one of ...

In this installment of the Lowe's home improvement series, host, Mike Kraft, one of Lowe's home improvement experts, demonstrates how to install lighting under your kitchen cabinets to make navigating your counter top easier. Mike lists all the necessary tools and materials you will need to complete this do-it-yourself at home project. You will learn tips and tricks for hanging the light fixtures, as well as how to run the wiring, so that the wires remain hidden from plain view.

This is a Computers & Programming video tutorial where you will learn how to startup configure a Mac. This is a very simple, easy and quick process. In order to change what programs start when you switch on your computer that is running on Mac, first go to ‘System Preferences’ from the drop down menu and then click on System Accounts. In the next box that pops up, go to ‘Login Items’. Here a list of programs will be displayed that run when you start up your computer. Here you check box next t...

In this how-to video, you will learn how to speed up your computer for free. You need a computer running a Windows operating system and access to the Microsoft Configuration Utility. First, open the start menu and click on run. Once this is doing, type in "msconfig" and click okay. Press the startup tab on the window that has opened. Here you will see a list of items that start when the operating system starts. You can uncheck the items that are not required to properly run the system. You ca...

It's exciting to get that reverse shell or execute a payload, but sometimes these things don't work as expected when there are certain defenses in play. One way to get around that issue is by obfuscating the payload, and encoding it using different techniques will usually bring varying degrees of success. Graffiti can make that happen.

Whether you're a celebrity or someone with something to hide, Facebook allows you to keep your "friends list" private so you can protect the identities of your Facebook friends. But it only kind of protects them.

In this video tutorial, viewers learn how to quickly copy a folder's content list in Windows. Begin by clicking on the Start menu and open the Run program. Then type in "cmd" to open the Command Prompt window. Now navigate the desired folder and type "dir | clip" beside it. Press Enter and it will automatically copy the directory to the clipboard. Essentially, it is a tool that will the command prompt command to the clipboard. This video will benefit those viewers who use a Windows computer, ...

If Internet Explorer 8 is being a nuisance in Windows 7 watch this video to learn how to uninstall it! Start by clicking your Start Menu, then to Control Panel and then to Programs. From there click Uninstall Programs. It will bring you to a list of all the programs that are currently on your hard drive. Next click Turn Windows features on or off. From there another list of programs will appear, but these programs are all Windows programs that come with Windows 7 Operating system. Watch the r...

In this video we learn how to find your IP address with the Command prompt. First, go to the start menu on your desktop. Then, find the run box and type in "cmd". After this, hit "enter" and then a black command prompt will show up on your screen. Next, type in "ip config" and then hit the enter button again. Now, a list of information will appear on the black screen. Look down the list to find the IP address listed on the page. Once you have this, you should write down your IP address and th...

Bucky from The New Boston serves up this Python video tutorial on how to program slice lists in Python. This is the program you use to write all of your Python code down. Slice Python!

Dull and drab bulleted lists are no longer necessary with the help of PowerPoint 2008 for Mac. When you make a bullet list in PowerPoint, you can now transform those boring text charts with actual visual charts and graphs and more. The Microsoft Office for Mac team shows you just how to convert text to a SmartArt graphic in this how-to video.

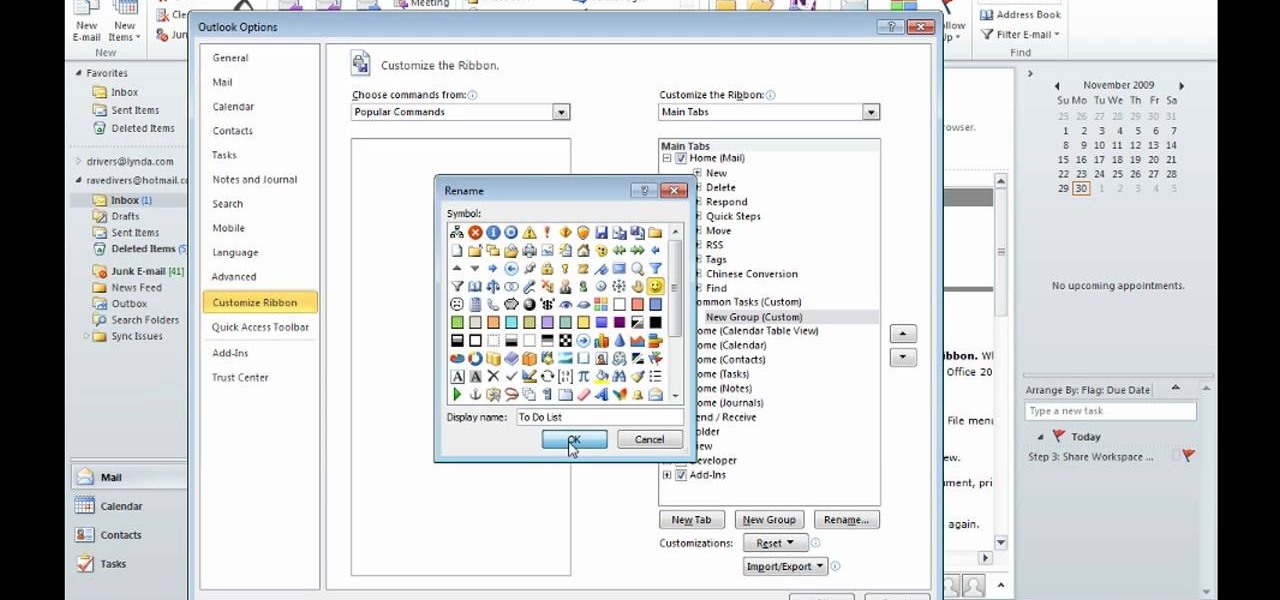
After you launch Outlook 2010 in your computer, you will see the Ribbon strip immediately in the main window. The button for writing a new e-mail is separated from a button for creating new items in the calendar, contact list or task manager. An independent Quick Steps section offers functions allowing you to move a message into different folders, to save it into a calendar as a meeting reminder, to quickly forward it to a chosen person or to more people and to forward it with a FYI note. If ...

Following someone on Twitter is an investment. You virtually agree to have their opinions, tirades, and hot takes spewed across your timeline. It can get annoying real quick if they're known to post controversial comments periodically. However, there are other ways to stay updated on someone's tweets without you having to hit the follow button and go all in.

When it comes to attacking devices on a network, you can't hit what you can't see. Nmap gives you the ability to explore any devices connected to a network, finding information like the operating system a device is running and which applications are listening on open ports. This information lets a hacker design an attack that perfectly suits the target environment.

A certain selection of applications on your Android device (both system and downloaded) start running as soon as your Samsung Galaxy Note 2 turns on, laboriously hammering away at whatever tasks they have to do.

For those of you still using a BlackBerry smartphone, this article will show you the tips and tricks to installing emulators and playing some classic Game Boy Advanced games on your device. You can find a few tutorials and videos out there on getting Game Boy Color or NES games on an Android device, but the most elusive mobile emulator is for Game Boy Advanced (GBA) on a BlackBerry.

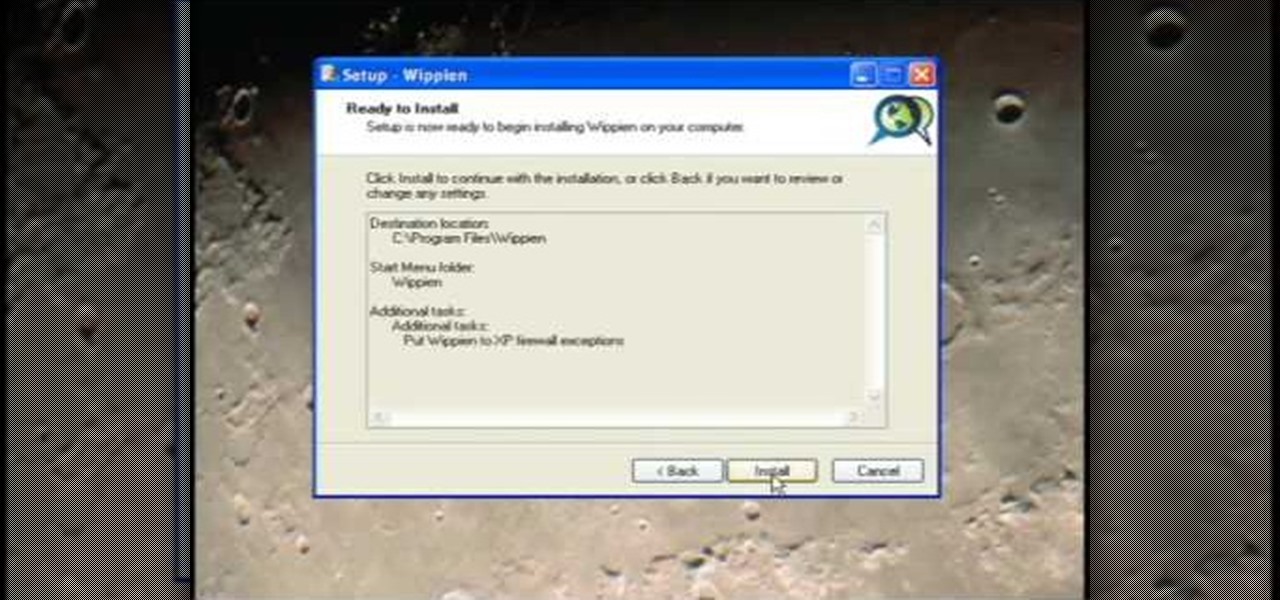
This video tutorial from ruralgeek shows how to set up and use Wippien VPN on Windows XP. First, download Wippien client from here: www.wippien.com.

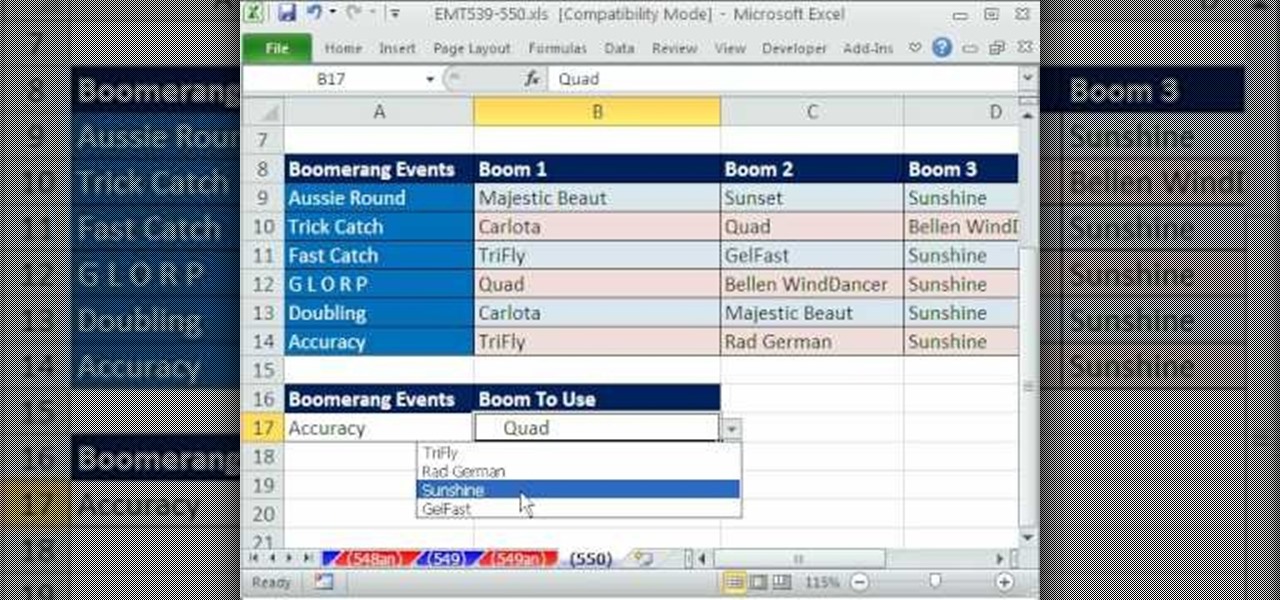
Excel dilettantes and seasoned Microsoft Office professionals alike may be surprised to learn that in Excel one can make a drop down list based upon a second drop down list (or, similarly, data validation list that is based on a second validation list).

This video explains how to add a bulleted or numbered list in Microsoft Word 2007. The shortcut to create a bullet-list is simple holding Shift and pressing the "A" key. After you hit the space bar or type a character the bullet will appear, and when you hit the Enter key it will continue the bulleted list. For numbering you just need to type the number you want and a dot after it and it should begin a numbered list. The list will continue if you press enter just like a bullet-list will. If y...

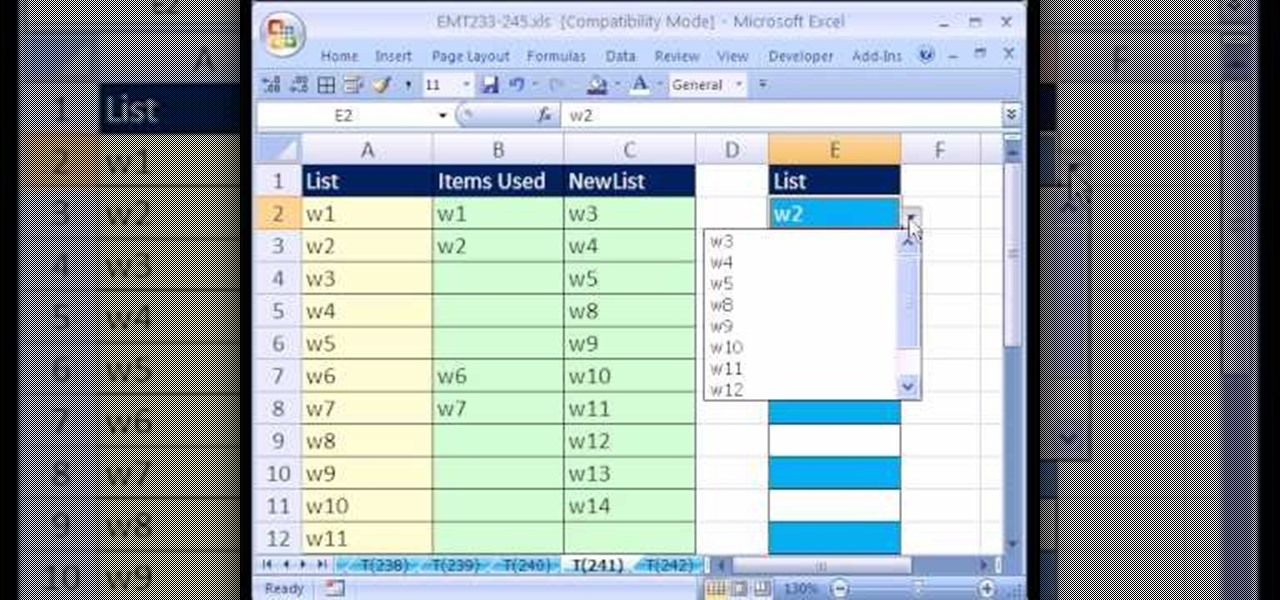
New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this MS Excel tutorial from ExcelIsFun, the 241st installment in their series of digital spreadsheet magic tricks, you'll learn how to create a data validation drop-down cell list where the list shrinks as you select values.

File permissions can get tricky on Linux and can be a valuable avenue of attack during privilege escalation if things aren't configured correctly. SUID binaries can often be an easy path to root, but sifting through all of the defaults can be a massive waste of time. Luckily, there's a simple script that can sort things out for us.

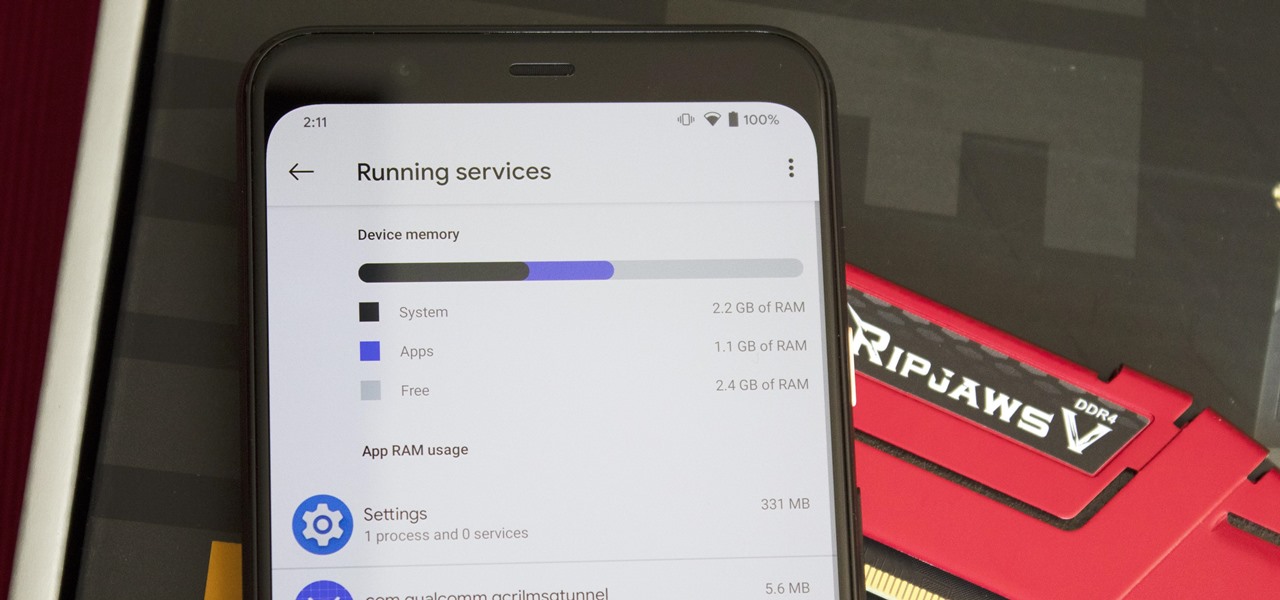
Not every app is designed well. With nearly 3 million apps on the Play Store and countless more that you can sideload from other sources, there are bound to be a few stinkers. And many of them do a terrible job using RAM.

Websites are often misconfigured in ways that allow an attacker to view directories that are not ordinarily meant to be seen. These directories can contain sensitive information such as private credentials or configuration files that can be used to devise an attack against the server. With a tool called Websploit, hackers can scan targets for these hidden directories without difficulty.

Just yesterday, Google announced that it is banning all apps that contain any form of lock screen ads. Today, they posted a list of the Best Apps of 2017 for the Play Store. Given the new policy of cracking down on apps with advertisements on the lock screen, you wouldn't expect to see one of those in the list of top apps. Unfortunately, that's exactly what happened — Google is promoting obvious adware in their list of best apps.

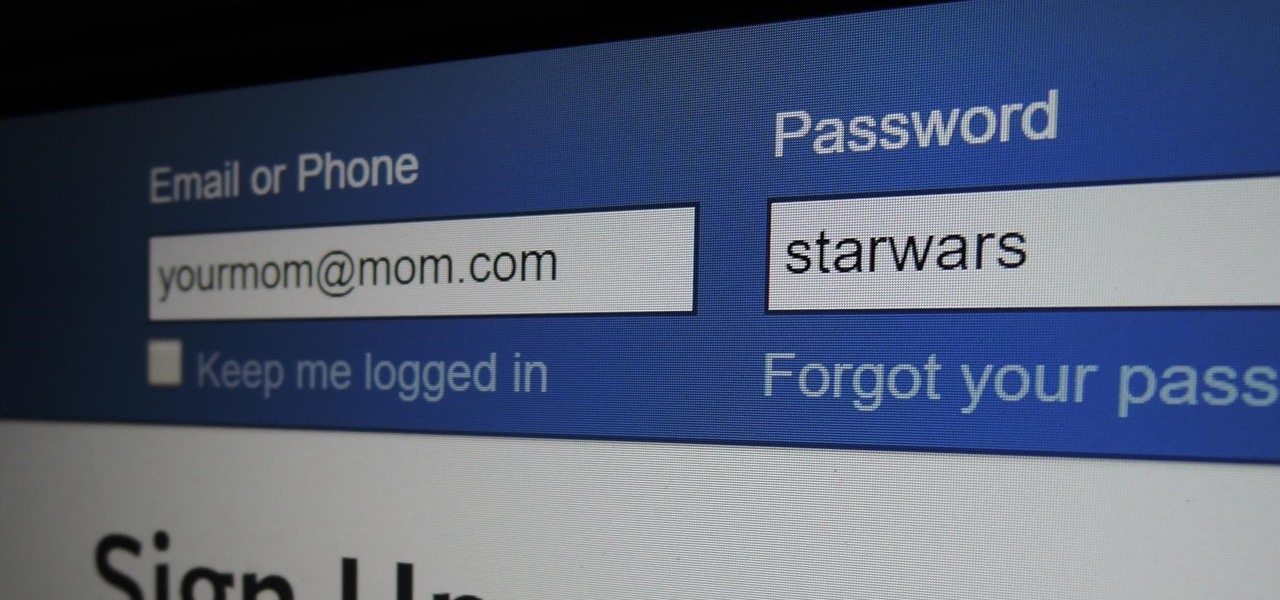
Some things never change. You'd think that with all the focus on web security, people might take the slightest precaution to keep their online activity private. Maybe there are more people suffering from Paula Poundstone's password troubles than we'd like to believe.